OpenSSL announced the release of an update to address a severe vulnerability in the library whose exploitation would lead to an infinite loop function and an eventual denial of service (DoS) condition. Although DoS attacks are not the most dangerous hacking variant, they can cause significant business disruption, long-term financial repercussions, and a severe loss of customer and user trust.
In the case of software like OpenSSL, the ubiquitous secure communication library used by many large online platforms. According to cybersecurity specialists, any vulnerability that affects the library can significantly impact a large number of users.
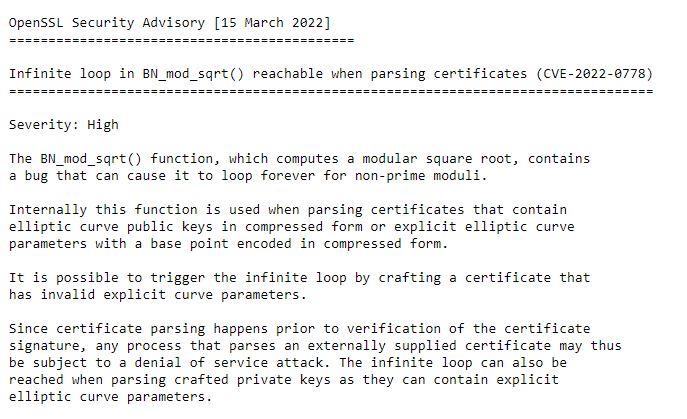
The OpenSLL problem exists due to an error in the function BN_mod_sqrt(), which if a certificate created for malicious purposes is delivered for analysis, will lead to the infinite loop. The certificate must contain elliptic curve public keys in compressed form or elliptic curve parameters with a base point encoded in compressed form to trigger the error. OpenSSL notes that the infinite loop can also be achieved by analyzing designed private keys, as they may contain explicit elliptic curve parameters.
The flaw lies in multiple implementations, including:
- TLS clients that consume server certificates
- TLS servers that consume client certificates
- Hosting providers that take certificates or private keys from customers
- Certification authorities that analyze subscribers’ requests for certification
Tracked as CVE-2022-0778, the vulnerability resides in all OpenSSL versions between 1.0.2 and 1.0.2zc, between 1.1.1 and 1.1.1n, and between 3.0 and 3.0.1. The vulnerability was reported by Google researcher Tavis Ormandy, who presented his findings to OpenSSL on February 24.
The corrected versions are 1.1.1n and 3.0.2, while only users of Premium versions 1.0.2 will be offered a solution up to 1.0.2zd. Because version 1.0.2 does not scan the public key during certificate analysis, the infinite cycle is a bit more complicated to activate than the other versions, although the attack is still possible. So far, no successful exploitation attempts related to this report have been detected.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











