Through The Zero Day Initiative (ZDI), the finding of a critical local privilege escalation vulnerability that could put millions of Samsung Galaxy S21 devices at risk was reported.
According to this report, the flaws allow local threat attackers to execute arbitrary code on affected smartphone models. Before the attack, malicious hackers must gain the ability to execute least-privilege code on the compromised system.
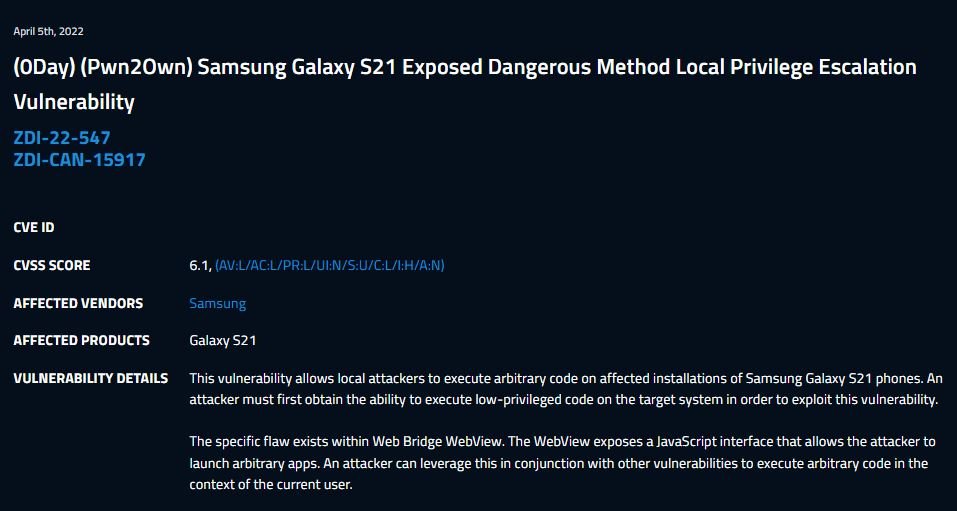
Apparently, the flaw resides within Web Bridge WebView. WebView exposes a JavaScript interface that allows threat actors to launch arbitrary applications; this flaw can be exploited along with other vulnerabilities to execute arbitrary code in the context of the current user.
The flaw was reported to developers in late 2021 and, in the absence of a functional patch, the researchers who reported it announced their intention to publicly disclose it as a zero-day vulnerability.
In addition, given the nature of the affected implementation and the type of attack, it is considered that the only recommended mitigation mechanism is to restrict interaction with the exposed application.
This Model of Samsung Galaxy is one of the company’s most popular smartphones, so the scope of successful exploitation could be huge. However, reports of the successful exploitation of the fault are still unknown.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











