A Microsoft security report details the finding of a set of vulnerabilities that would allow threat actors to escalate privileges on Linux systems in order to inject ransomware, backdoors, and other severe threats. The flaws were identified as Nimbuspwn and their exploitation would trigger access to root privileges on compromised systems.
Nimbuspwn refers to the CVE-2022-29799 and CVE-2022-29800 flaws, which reside in networkd-dispatcher, a component that sends connection state changes on Linux machines. The flaws were discovered during an analysis of messages on the system bus, which led to a review of the code flow for networkd-dispatcher.

Microsoft researcher Jonathan Bar Or mentions that this set of flaws involves issues such as path traversal errors, symbolic link race conditions, and time-of-check-time-to-use (TOCTOU) race conditions. Additionally, during analysis it was observed that the network-dispatcher daemon was running with root privileges at system boot time.
Microsoft discovered that the daemon used a method called “_run_hooks_for_state” to discover and run scripts based on the state of the detected network.
The logic of this method includes returning executable scripts owned by the root user and the root group in the “_run_hooks_for_state” directory. The method executes each script in the above location using subprocess.Popen, while providing custom environment variables.
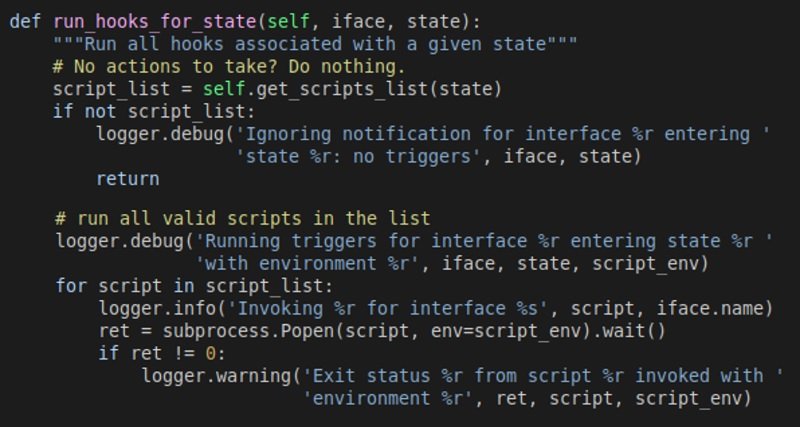
The execution of “_run_hooks_for_state” is what leads to the appearance of these security problems, as reported by Microsoft. Exploitation of Nimbuspwn would allow a threat actor with reduced privileges on the affected Linux system to escalate their privileges to the root level by sending arbitrary signals.
A description of the steps for a successful exploitation is shown in the following diagram, divided into three attack steps:
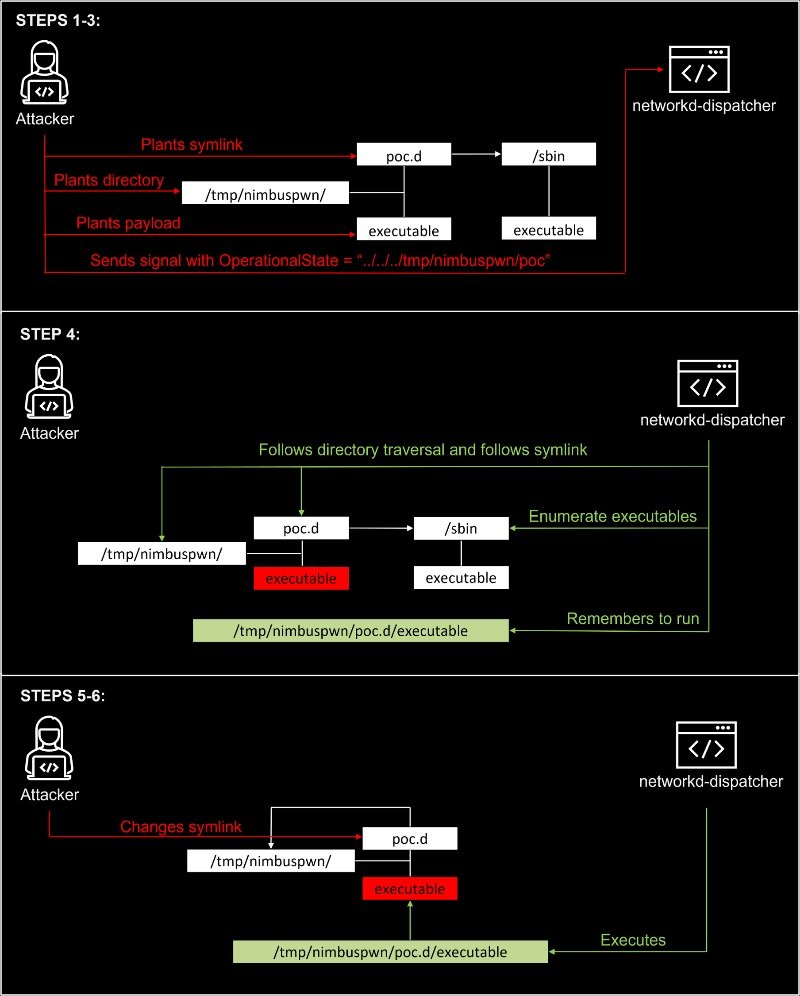
Microsoft specifies that successful exploitation requires planting various files on the affected system.
The report concludes by mentioning that there are many environments where the attack is feasible, including Linux Mint because the systemd-networkd service which normally has the bus name “org.freedesktop.Network1” is not started on boot by default. .
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











