In its latest security advisory Cisco announced the fix of several flaws in its NFV Infrastructure Software (NFVIS), a network virtualization solution for virtual network function (VNF) management. Two of the fixed flaws are considered critical and could be exploited by threat actors for the execution of commands with root privileges and for guest virtual machine evasion attacks.
Through its Product Security Incident Response Team (PSIRT), the company mentions that at the moment no publicly available code for the exploitation of the flaw has been detected, nor have active exploitation attempts.
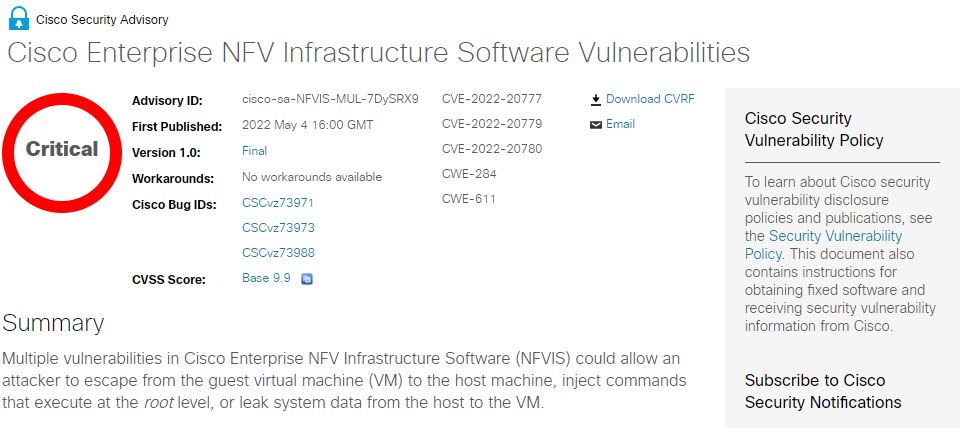
The first of the critical flaws was tracked as CVE-2022-20777 and resides in Cisco NFVIS’ Next Generation Input/Output (NGIO) feature. According to the report, the flaw exists due to inadequate guest restriction, which would allow authenticated threat actors to escape the virtual machine and gain root access to the host for the deployment of fast attacks that do not require interaction from the target user.
According to Cisco, the flaw could be exploited by sending an API call from a virtual machine that will run with root-level privileges on the NFVIS host. A successful attack could allow hackers to take full control of the NFVIS host.
On the other hand, CVE-2022-20779 was described as a command injection vulnerability in the Cisco Enterprise NFVIS image registration process that exists due to improper input validation. An unauthenticated malicious hacker could exploit the flaw remotely to inject commands with root privileges into the host during the image registration process; unlike the previous attack, exploiting this flaw requires interaction from the affected user.
Hackers could exploit this flaw by tricking the administrator of a target host machine into installing an image with specially crafted metadata, or that would allow the execution of commands with root privileges in the virtual machine registration process.
The vulnerabilities reside in Cisco NFVIS v4.0 and earlier, and were fixed with the release of v4.7.1, so users of affected deployments are advised to patch them as soon as possible. Alternative solutions for these vulnerabilities are unknown at the moment.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











