In early 2022, Microsoft addressed CVE-2022-22005, a remote code execution (RCE) vulnerability that used website creation features in SharePoint, releasing a security patch. Even though the flaw had already been fixed, a security researcher found a new way to exploit the deserialization bug by uploading malicious files to the server.
Many languages use serialization and deserialization to pass complex objects to servers and between processes. If the deserialization process is not secure, attackers will be able to exploit it to send malicious objects and execute them on the server. Nguyễn Tiến Giang, a security researcher at StarLabs, found that when servers are configured in a certain way, they are prone to deserialization attacks, which would eventually lead to code execution.
In his blog, the expert explains that hackers can exploit the bug by creating a SharePoint List on the server and loading a string of malicious devices with the deserialization payload as a PNG attachment. By sending a processing request for the uploaded file, the attacker will trigger the error and execute the payload on the affected deployment.
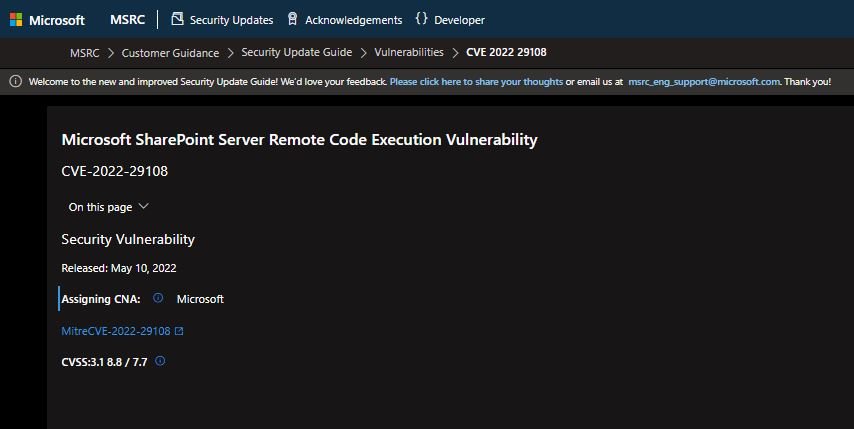
The good news is that the flaw can only be exploited by authenticated threat actors, plus a default disabled setting is required. This variant of the vulnerability, tracked as CVE-2022-29108, was addressed in Microsoft’s May patch.
The expert found the flaw while analyzing CVE-2022-22005, finding that there was another way to trigger the attack: “Actually, this error is very easy to detect. There was a publication about it March; you just have to follow the instructions in that post and people can easily detect the new variant of CVE-2022-22005. It’s like drinking an old wine from a new bottle,” the expert joked.
Finally, the researcher known as hir0ot, who had published a detailed analysis on CVE-2022-22005, mentions that there are two main ways to correct deserialization failures: by limiting the endpoints that deserialize untrusted data, or by using a folder of a type based on a whitelist.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











