A well-known tool in the security sector for classifying and identifying malware samples is YARA. Avast just gave the open-source community two tools. YARA Language Server and YaraNG are technologies linked to YARA.
Although debugging YARA rules after they have been developed might be difficult, writing them can be tough. Consider a scenario in which your YARA rule fails to match the expected samples. It appears to be an issue, but how can you identify the cause and resolve it? What aspect of the illness is the bug? How do you tackle this circumstance as a writer?
Users (in this instance malware analyzers) would anticipate having access to at least sufficient tooling for writing YARA rules. Real life, however, is a very other story. Very few solutions exist that offer a small number of functionalities, and many of these are either paid or poorly maintained.
A large majority of users only utilize plain text editors, occasionally even without syntax highlighting. Users were left to manage regulations on their own, which was a laborious undertaking. This absence of tooling had an adverse effect on the quality of the created regulations as well as on users. Avast sought to alter it and offer a contemporary and effective way to read and write YARA, preferably in your preferred editor.
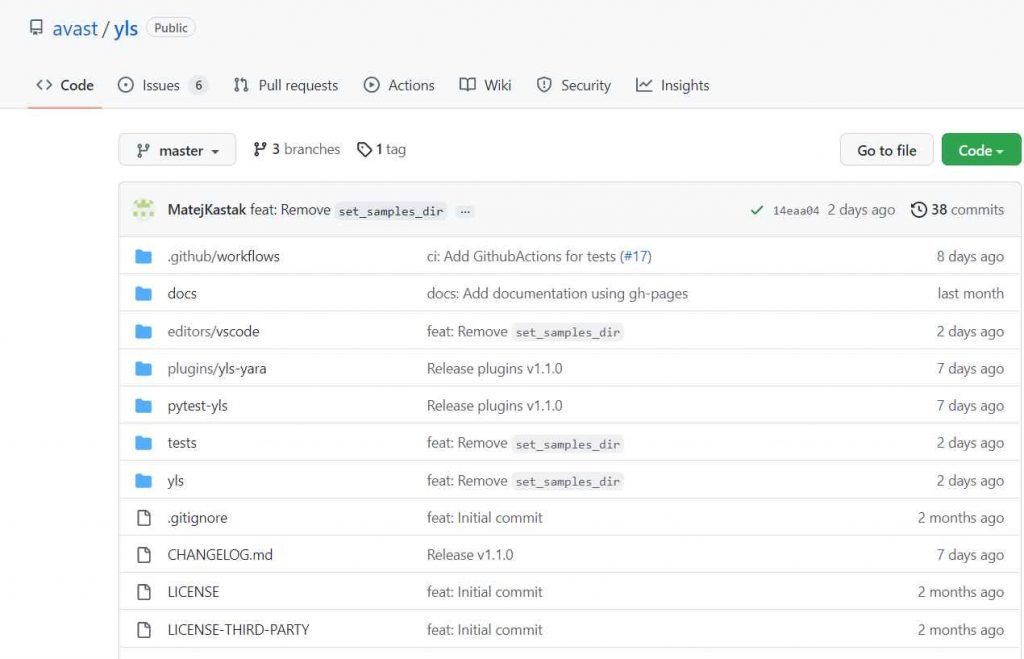
YLS enters the scene in this situation. It forms the basis of the solution we are opening-sourcing right now. The sources are accessible at avast/yls. Malware analysts have been working on it for more than two years, and Avast has successfully employed it. It adds a number of long-needed features to make writing, modifying, and interpreting YARA rules easier and more effective.
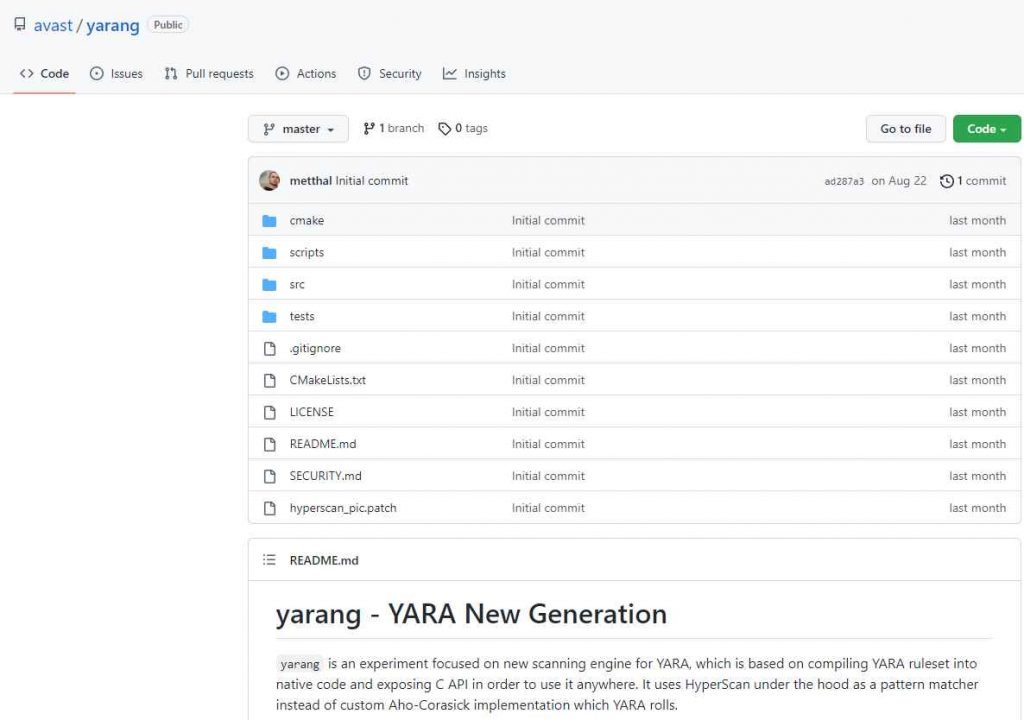
The company also released the YARA Language Server as open source, and it has just released YaraNG, a new version of the YARA scanner.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











