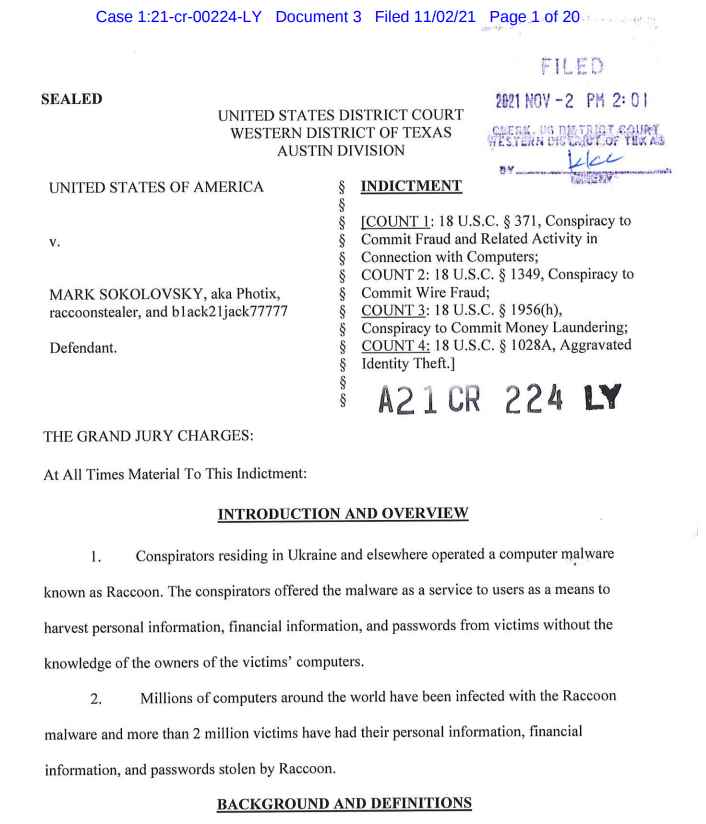
The United States Department of Justice has announced that a Ukrainian programmer has been charged, among other things, with computer and bank fraud in the United States. This is Mark Sokolovsky, one of the key figures behind Raccoon Infostealer, a well-known malware capable of infecting millions of computers.

This malware was rented to cybercriminals for $200 per month, paid in cryptocurrency, and installed on victims’ computers through various well-known techniques, including phishing emails. Once inside, the malware stole personal data – email addresses, bank accounts and credit card numbers – to commit financial crimes. The authorities have stated that it is one of the biggest cases of cybercrime in recent years.

The young Ukrainian faces more than 20 years in prison if he is finally found guilty. At the moment, he has been detained in the Netherlands for months awaiting possible extradition to the United States, to which he has appealed. If he is finally extradited, the US justice system will try him for computer fraud, electronic fraud, money laundering and identity theft.
Sokolovsky, 26, was one of many men who fled Ukraine when the armed conflict with Russia began. Logically, he did not want to go to the battlefront. So, together with his girlfriend, he left Kharkiv for Amsterdam by car. They passed through Poland and Germany, but did not stop until they reached the capital of the Netherlands, where they believed they were safe.

But they weren’t. The Ukrainian programmer’s iCloud account linked him to Raccoon Infostealer. Sokolovsky made the mistake of linking his iCloud to the Gmail account he used to log into Raccoon. That’s not all, because thanks to this account they were also able to see his face: they got a photo of Sokolovsky strutting around with several wads of bills.
This iCloud account associated with Sokolovsky began to be monitored. When the war came, the investigators were able to see him and his partner leaving the country. There are even images of both crossing the border with a high-end car. It is suspected that they may have bribed someone to let them through to Poland.
They already had the face and access to the location. But, in addition, the couple was showing their new life in Amsterdam, their final destination, through social networks. Within days of starting posting photos, Sokolovsky was arrested and Raccoon Infostealer stopped working thanks to the efforts of the Netherlands and Italy.
When Sokolovsky, who was known as raccoonstealer, Photix and black21jack77777, was arrested, the hackers involved in Raccoon Stealer claimed that they had ceased their activity because not one of its main developers had been killed during the Ukraine invasion, which was not true.
However, Raccoon Stealer returned to the fray in early June with the release of a new version with new data theft capabilities.
The FBI has so far managed to recover 50 million unique credentials, including email addresses, bank account logins, cryptocurrency addresses, and credit card numbers.
According to court documents, the data recovered by the feds included login information for various US companies and members of the military with access to military systems. But they believe that there is still much more stolen data that has not been recovered and they continue to work on it.
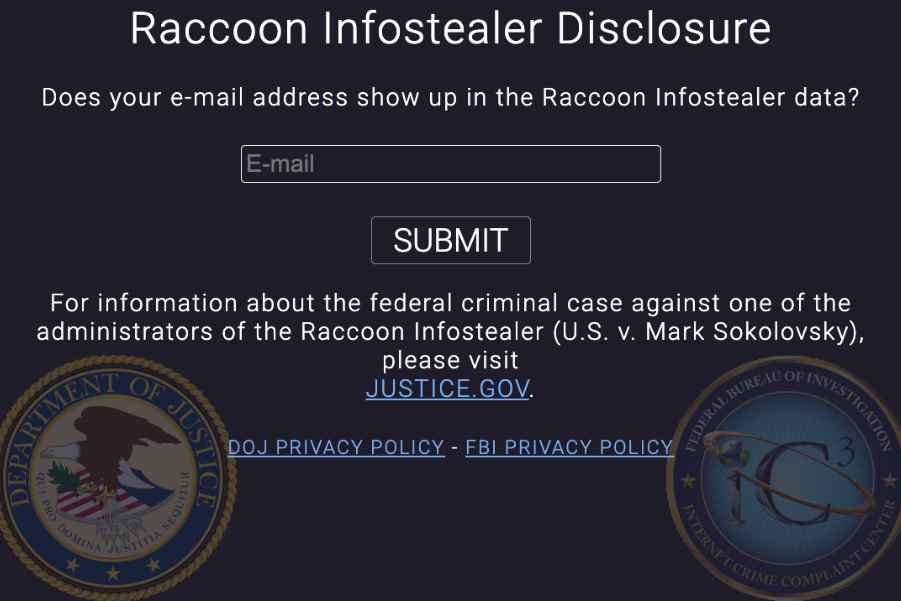
For victims, the agency has created a website, called raccoon.ic3.gov, where anyone can enter their email address to find out for sure if any of their data is part of the information stolen by the malware. In the event of being attacked by this malware, the FBI will send an email to that address to inform the user.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











