Mastodon has been under the limelight as a result of the exodus of former Twitter users who left the platform in response to the turbulence brought on by Elon Musk’s purchase of Twitter. For many members of the infosec community who have switched from tweeting to “tooting” on the site, it has become their go-to hangout.

Security expert Lenin Alevski cautions that many instances of the social media network Mastodon are susceptible to configuration flaws. Alevski just discovered that the infosec.exchange Mastodon instance was uploaded to storage buckets without any access constraints. By exploiting these vulnerabilities, he was able to replace everyone’s profile image with a meme stored in infosec.exchange Mastodon instance .
A brief glance at the page’s source code indicates that https://media.infosec.exchange/infosecmedia is the source of the material. This looks like an AWS S3 xml response, and the response also says “minio” to indicate that MinIO is being used.
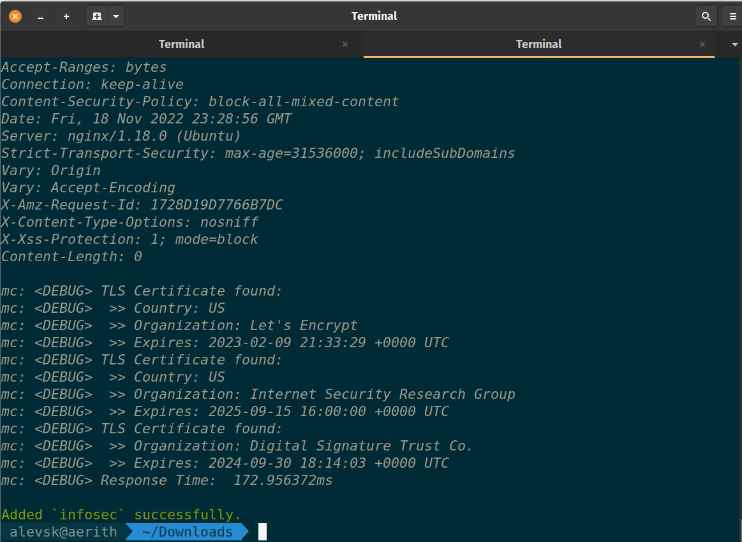
Users upload stuff to MinIO buckets.
In order for the browser, or indeed any other client, to access those resources, buckets must have anonymous read access.
The flaws enable A program like the MinIO Client can be used by anybody to query such resources. To get data from the buckets, s3 clients don’t require any kind of authentication. He was able to list all the content thanks to this. There were other files in there that he could access using anonymous credentials, similar to a Directory Traversal vulnerability.
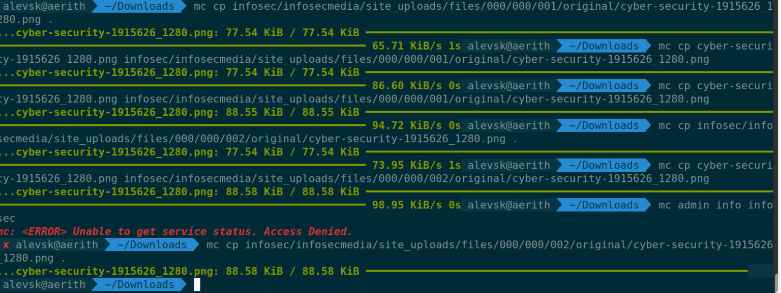
Any threat actor can get all the files on the server exploiting this vulnerability, including those exchanged via Direct Messages, delete all of the server’s files and changing everyone’s profile image is also possible, but it was also feasible to modify all of the current files.
Mastodon has fixed this flaw but this vulenerblity or other similar ones might exists in other systems of Mastodon.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











