Docker is a technology for containerization, while Kubernetes is a tool for orchestrating container deployments. In the subsequent subsections, we will discuss a variety of open-source tools that really are useful for securing Kubernetes clusters. These open source tools involve code snippets that will help with static scanning of Docker images, security auditing, hardening Kubernetes clusters, and incorporating runtime security. Some of the most popular Kubernetes clusters managed by cloud providers include AWS EKS, Azure AKS, and Google CKE. The following is a list of open source tools that may be used to do security scans and that can be incorporated into your CI/CD pipeline in order to analyze images while your apps are being built:
1. Analysis of Vulnerability and Exposure Using Clair
Clair is a vulnerability static scanning tool that is free source and designed for containers. The application supports a variety of deployment strategies and excels in situations requiring a high level of scalability and availability. Clair is compatible with REST APIs and offers scan reports in HTML format. The CVEs database that was developed as part of the Clair project is used by the Amazon Elastic Container Registry (Amazon ECR), which then produces a list of discoveries.
2. Using Trivy to find security holes
Trivy is a scanning tool that is available as open source and is an ideal option for teams who are interested in doing static application security testing as well as rapid scans. In addition to detecting configuration problems and providing complete vulnerability identification for operating systems, infrastructure as code files, and language packages, it is also used to identify vulnerabilities in code files. Additionally, Trivy is able to automatically update its vulnerability database.
After running a Trivy scan, you will be presented with a list of vulnerabilities, along with an indication of the severity of each vulnerability and a CVE number, if one is available.
3. Using kubeaudit to do audits on Kubernetes
Kubeaudit is an open source tool that was developed by Shopify. It is used to audit Kubernetes installations against standard security measures including the following:
run in a non-root capacity
Use a root filesystem that can only be read.
Get rid of frightening capabilities and don’t introduce any more.
don’t run privileged
4. Using Kubescape for Security Testing
Kubescape is a program that can assess whether or not Kubernetes is installed in line with practically all key compliance standards, such as the NSA-CISA and MITRE ATT&CK®, in addition to DevSecOps best practices. Kubescape is an open source tool. Integration with Continuous Integration (CI) technologies is also possible with Kubescape.
5. CIS Benchmarking Utilizing the Kube-Bench Platform
Kube-bench is an open source program that determines whether or not Kubernetes is implemented in the most effective manner in accordance with the CIS Kubernetes Benchmark. This benchmark includes a collection of Kubernetes security best practices. As a result, kube-bench is most effective when it is necessary to scan just for the sake of CIS benchmarking.
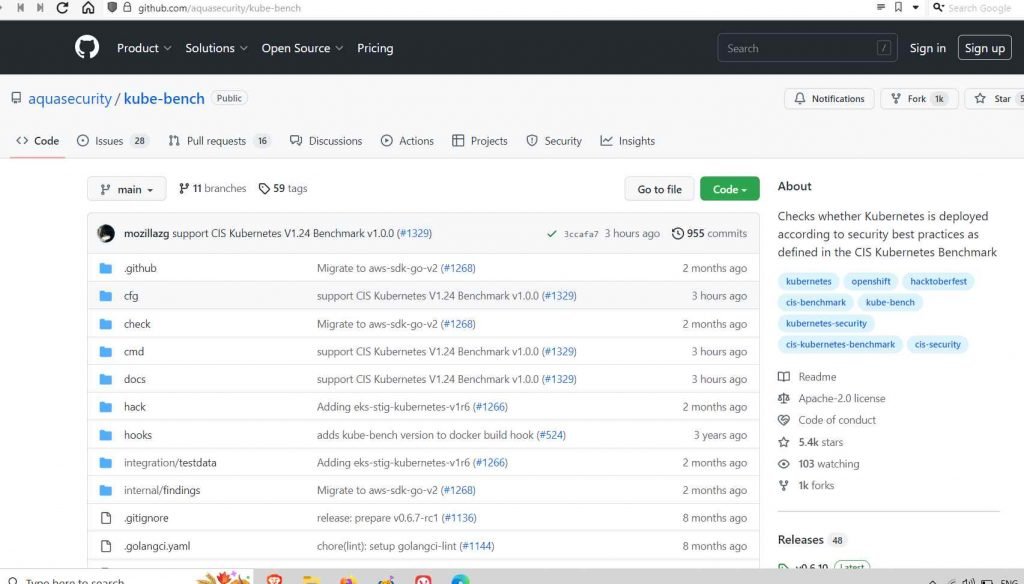
Within a pod, you are able to execute the kube-bench program. The GitHub repository includes job-cloud provider>.yaml files that are cloud-specific, and kube-bench will automatically select which test set to run depending on the version of Kubernetes that is currently running on the computer.
6 .Penetration Testing Utilizing the Kube-Hunter
Kube-Hunter is an open – sourced penetration testing tool that was written in Python. It allows you to design custom modules that can be performed from local workstations, inside the cluster, and remotely in both active and passive mode. Kube-Hunter was developed by Google.
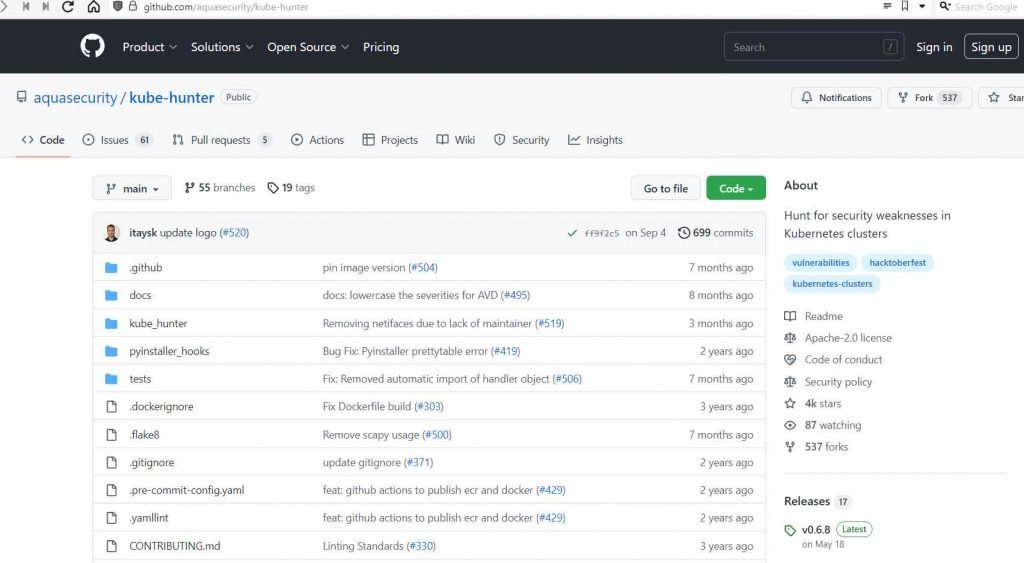
When running in active mode, kube-hunter will search for and then further exploit any vulnerabilities it finds. Additionally, you have the option of running kube-hunter on a staging environment in the form of a malicious pod, which may simulate a true attack in its own right.
Each of the three tools discussed previously, kubeaudit, Kubescape, and kube-hunter, generates a comprehensive report that includes information on misconfigurations, vulnerabilities, checks that were skipped, insecure behaviors, and more.
7. Real-Time Protection Utilizing Sysdig Falco
An open source runtime security solution known as Sysdig Falco is deployed across Kubernetes clusters for the purpose of continuous risk and threat detection. The technology functions as a surveillance camera that monitors for unusual activity, changes in configuration, intrusions, and stolen data in real time. For the time being, Sysdig Falco is the only open source solution for Kubernetes runtime security that has been authorized by the CNCF.
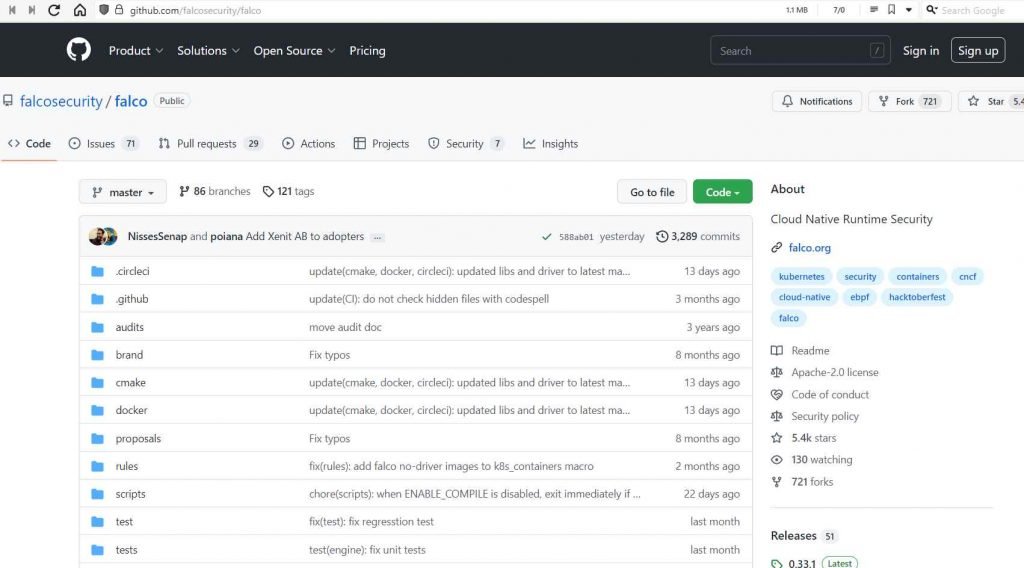
Falco, which allows you to write your own plugins and contains all of the major features found in its commercial tools, consumes the raw stream of system call information utilizing drives such as a kernel module or an eBPF probe. Additionally, Falco gives you the ability to write your own plugins. Falco has the capability to operate as a daemon on Kubernetes Nodes. In this mode, it is able to monitor and send real-time security warnings in JSON format through stdout, HTTP hooks, and syslog.
8. Docker Image Analysis Using Static Scanning
A Docker image may be created by following the instructions in a file known as a Dockerfile, which is an ordinary text document that includes a set of instructions. In addition, containers are the instances of Docker images that are now operating, and Kubernetes supports the Docker runtime.
Before attempting to publish your Docker images to a Kubernetes runtime environment, it is strongly advised that you do a security vulnerability assessment on them. Shifting to the left like this can help you avoid assaults on your supply chain and increase your security.
Docker Engine has at this point included Synk’s scanning capabilities in order to find vulnerabilities in the images. The list of CVEs and recommendations is what is produced as a result of doing the scan.
As you can see, the ecosystem of free source technologies that may be used to increase Kubernetes security is rather robust. You can execute automated scans, CI integrations, runtime security, penetration testing, and audit checks using one of the many tools that are accessible to you on GitHub. Utilize this article as a reference guide while you put your Kubernetes security program into action to ensure the safety of your apps, network, and data.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











