Samba is a free software re-implementation of the SMB networking protocol that offers file and print services for a variety of Microsoft Windows clients. It is also capable of integrating with a Microsoft Windows Server domain, either as a Domain Controller (DC) or as a domain member. Samba was developed by the Samba Development Team and is distributed under the GNU General Public License. The program is compatible with almost all Unix-like operating systems, including Linux, Solaris, AIX, and the many BSD variations. It is also compatible with Apple’s macOS Server and macOS client (Mac OS X 10.2 and greater).
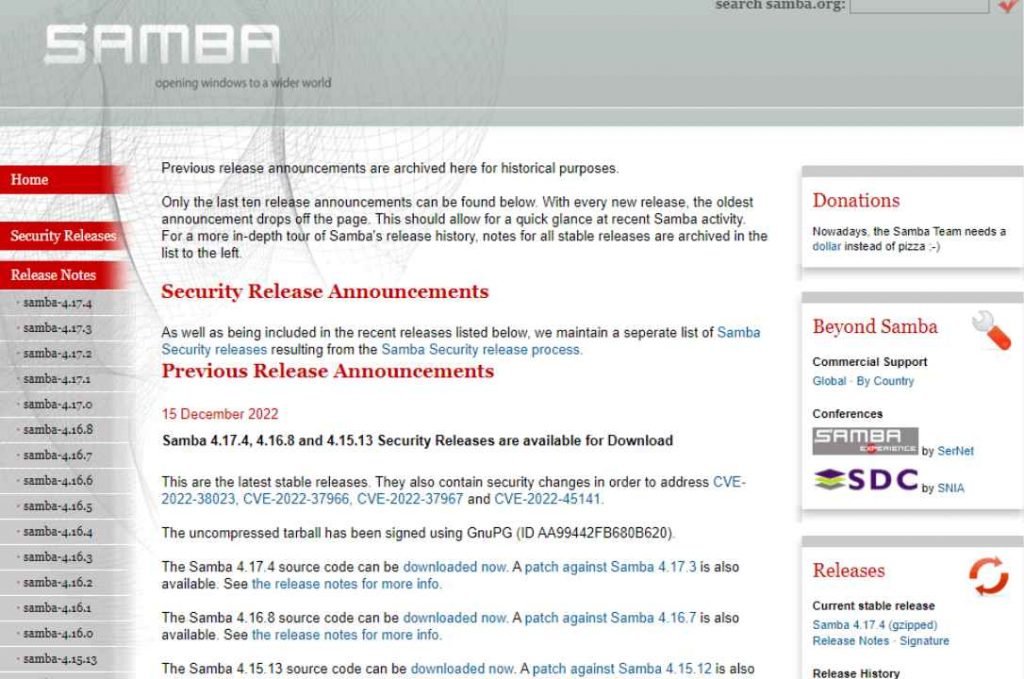
Samba has issued patches to fix various vulnerabilities, some of which may be abused to take control of affected computers. These vulnerabilities are tracked as CVE-2022-38023, CVE-2022-37966, CVE-2022-37967, and CVE-2022-45141, respectively.
CVE-2022-38023
Since the “RC4” protection of the NetLogon Secure channel employs the same techniques as the rc4-hmac cryptography used in Kerberos, it is reasonable to presume that it, too, is insecure. The fact that the secure checksum is not encrypted is a flaw in the NetLogon Secure channel.
Generated as HMAC-MD5(MD5(DATA),KEY), which means that an active attacker who knows the plaintext data might produce a different selected DATA, with the same MD5 checksum, and replace it into the data stream without being noticed. This is because HMAC-MD5 is a hash function.
CVE-2022-37966 – This is the Samba CVE for the Windows Kerberos RC4-HMAC Elevation of Privilege Vulnerability that was discovered by Microsoft on November 8th, 2022. Despite the fact that all recent Kerberos implementations offer the aes256-cts-hmac-sha1-96 cipher, a Samba Active Directory DC will issue weak rc4-hmac session keys for usage with modern clients and servers. These session keys will be used for communication. Kerberos encryption types = legacy will require rc4-hmac as a client on Samba Active Directory DCs and members, even if the server supports aes128-cts-hmac-sha1-96 and/or aes256-cts-hmac-sha1-96. This is the case even if the server supports aes256-cts-hmac-sha1-96.
CVE-2022-37967 – Windows Kerberos has a vulnerability known as CVE-2022-37967, which allows for the elevation of privilege. It is possible for a service account that has the special limited delegation authorization to fake a ticket that has a higher level of authority than the one it was first given.
CVE-2022-45141 – Since Microsoft published the Windows Kerberos RC4-HMAC Elevation of Privilege Vulnerability on November 8 2022, and since RFC8429 states that it is safe to presume that rc4-hmac has a low level of security, CVE-2022-45141 has been assigned to it. Despite the fact that the destination server supports greater encryption, vulnerable Samba Active Directory DCs will continue to send tickets encrypted using rc4-hmac (eg aes256-cts-hmac-sha1-96).
Samba has addressed the aforementioned vulnerabilities with the security releases version 4.17.4, 4.16.8, and 4.15.13.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











