The American corporation Lexmark International, Inc. is a privately owned business that specializes in the production of laser printers and other image goods.
The researcher found that the product is susceptible to two vulnerabilities, either of which can be exploited by an adversary to copy file data from a source path to a destination path or to induce the server-side application to make requests to an unintended location. Both of these vulnerabilities are possible due to the fact that the product is vulnerable to both of these vulnerabilities. According to the specialists, the printer has two vulnerabilities that enable an authorized hacker to upload arbitrary files and run code with elevated privileges. Both of these vulnerabilities may be exploited by a malicious user.
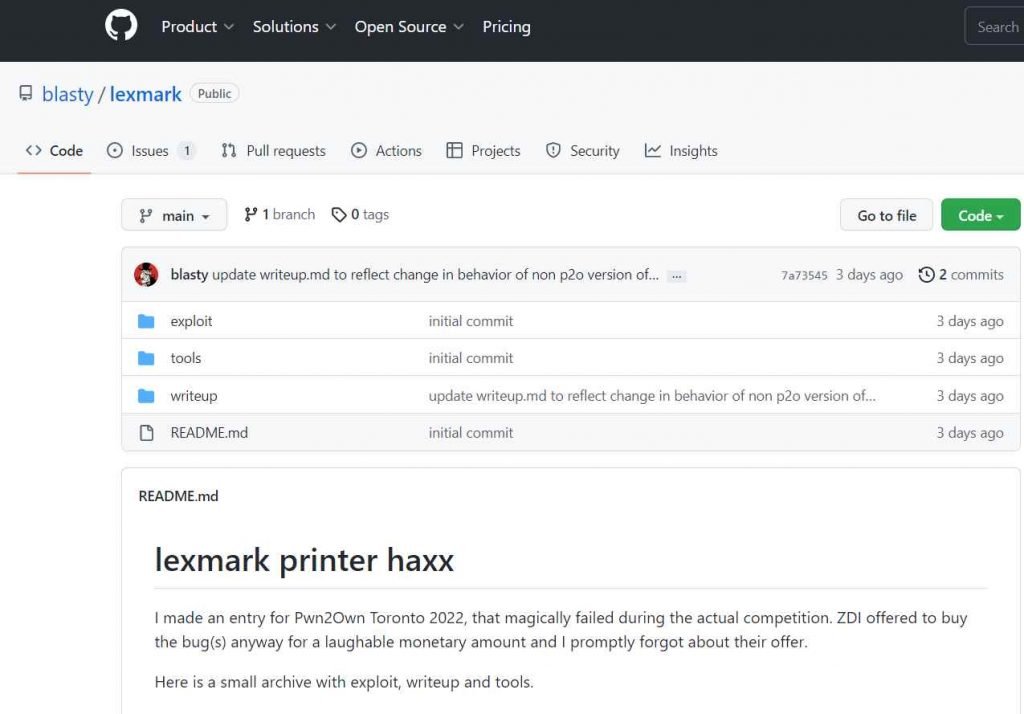
He published the code on Github that had a proof-of-concept (PoC) exploit for each of the four vulnerabilities. These vulnerabilities make it possible for an adversary to seize control of a vulnerable device.
According to the findings of the researcher, an attack may be carried out that compromises the device by exploiting all four of its vulnerabilities simultaneously.
The proof-of-concept attack has been successfully tested against a Lexmark MC3224adwe printer using the most recent version of the firmware, CXLBL.081.225; nevertheless, it is claimed to operate successfully against other printers and photocopiers as well.
The security flaw that was discovered in Lexmark’s printer devices has not been fixed.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











