The Goose Tool is a new free tool that may assist network defenders in identifying possibly malicious activities in Microsoft Azure, Azure Active Directory, and Microsoft 365 environments. It was developed by CISA and is available on their website. The Unidentified Goose Tool, which was developed with assistance from Sandia National Laboratories, provides network defenders with unique authentication and data collection techniques that may be used when they are investigating and analyzing their Microsoft cloud services.
According to CloudVulnDB, an open project that tracks vulnerabilities affecting major cloud providers, there is a lengthy record of severe security flaws plaguing Redmond’s flagship Azure, and defenders have long complained about the lack of insight into possible infections.
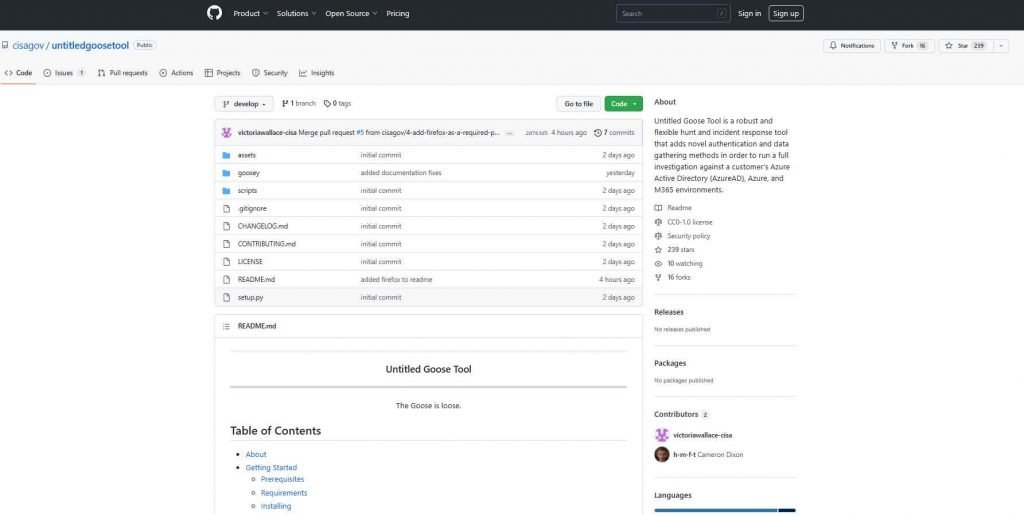
The Untitled Goose Tool is a powerful and adaptable investigation and incident response instrument. When network defenders interrogate and analyze the environments of Microsoft Azure, Azure Active Directory (AAD), and Microsoft 365 (M365), the tool provides them with novel authentication and data gathering methods to use in the process. These methods can be used to detect potentially malicious activity. Goose, which was created by CISA in collaboration with Sandia National Laboratories, may be downloaded for free from the CISA GitHub Repository.
Network defenders are encouraged to use the Untitled Goose Tool in order to carry out the following tasks: • Export and review AAD sign-in and audit logs; M365 unified audit log (UAL); Azure activity logs; Microsoft Defender for IoT (internet of things) alerts; and Microsoft Defender for Endpoint (MDE) data for suspicious activity.
• Conduct investigations into AAD, M365, and Azure setups, as well as query and export related data.
While trying to probe a big M365 tenant using the UAL, network defenders may discover that manually collecting all events at once is not a practical option. Untitled Goose Tool implements creative data collection strategies by using unique mechanisms. The following are some of the capabilities that network defenders have while using this tool: • Extract cloud artifacts from Microsoft’s AAD, Azure, and M365 environments without doing further analyses.
• Use the goosey grazing method to do time bounding on the UAL.
• Use goosey honk to extract data while staying within the allotted time limits.
• Inquire into and gather data making use of comparable time bounding capabilities for MDE data.
Compatibility
The user’s Azure, Azure AD, and M365 environments may all be used with the Untitled Goose Tool.
Prerequisites
Python version 3.7, 3.8, or 3.9 is required to run Untitled Goose Tool. The CISA suggests using this technology inside a virtual setting.
The government organization said that cloud network administrators may use the tool to extract cloud artifacts from Microsoft’s AAD, Azure, and M365 systems without having to run any further analyses.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











