A serious flaw has been found in WooCommerce, a popular plug-in for managing online businesses that are built on the WordPress platform. This flaw might enable cybercriminals to take control of websites. Nevertheless, the WooCommerce team has provided fixes, and attackers are able to reverse-engineer the patch. Technical specifics concerning the vulnerability have not yet been disclosed. There are presently approximately 500,000 active installations of the WooCommerce Payments plug-in, which is the component that includes the vulnerability. The creators of WooCommerce have stated that managed WordPress hosting providers such as WordPress.com, Pressable, and WPVIP have automatically updated websites that are hosted on their platforms. But, if the other websites don’t already have automatic updates turned on, the administrators of those websites should immediately apply the update that is specific to their version.
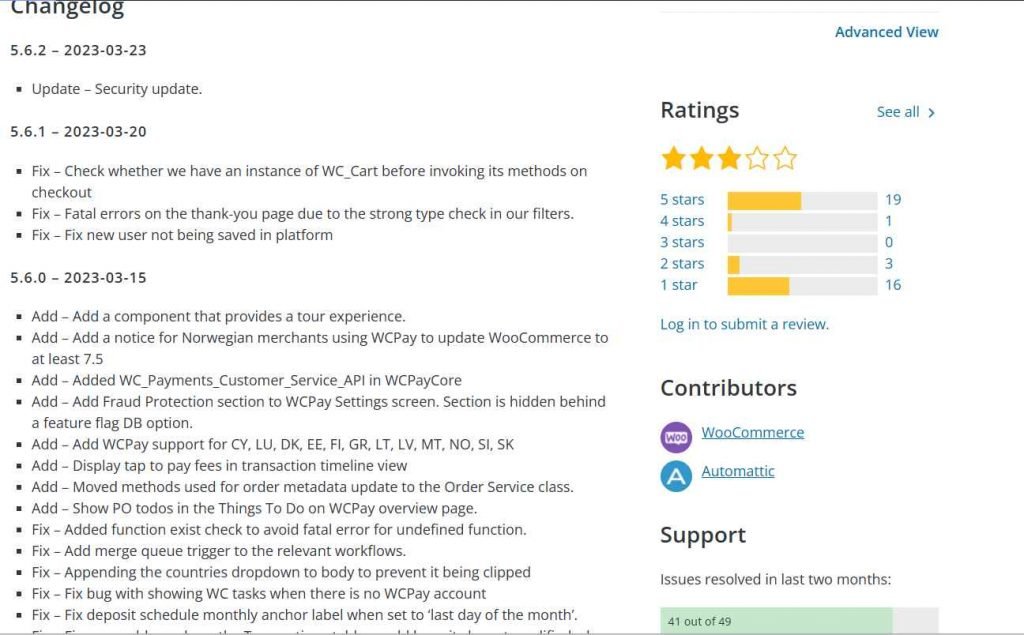
Any versions of WooCommerce Payments that were created after 4.8.0, which was published at the end of September, are susceptible to the vulnerability. The following updated versions were made available by Automattic: 4.8.2, 4.9.1, 5.0.4, 5.1.3, 5.2.2, 5.3.1, 5.4.1, 5.5.2 and 5.6.2.
As soon as a patched version of WooCommerce has been installed, administrators of websites using WooCommerce should verify their sites for any unusual admin users or postings. The creators of WooCommerce suggest that, in the event that suspicious behavior is discovered on a website, the passwords of all administrative users on the site be changed, in addition to any API credentials for WooCommerce and payment gateways.
According to the creators of WooCommerce, “WordPress user passwords are hashed using salts, which means the final hash value is incredibly tough to decipher.” “This solution uses a salted hash to safeguard not just your password as an administrative user but also the credentials of all other users on your website, including customers. While it is conceivable that an attacker took advantage of this vulnerability to acquire a hashed version of your password that was saved in your database, the hash value itself should be impossible to decipher so that your passwords remain secure and cannot be used in an unauthorized manner.” Nevertheless, it is important to note that this only applies to the hashes of passwords that are saved using the default authentication method that comes with WordPress. It’s possible that some other plug-ins will make use of the database to store credentials, tokens, and API keys without hashing them first. Administrators need to examine what potentially sensitive information is stored in their databases and rotate all of that information.
WooCommerce has said that it does not think this vulnerability was utilized to compromise shop or customer data. Nonetheless, merchants may wish to watch how this event evolves since it might affect their business. The issue was reported in confidence via the bug bounty program that Automattic maintains on HackerOne. Even if the technical particulars have not been made public just yet, the disclosure policy states that this should happen within the next two weeks. Nevertheless, the experts from Sucuri have previously pointed out that the vulnerability was probably in a file named class-platform-checkout-session.php, which seems to have been fully deleted from the version that has been patched. Because these competent hackers already know where to search, it is consequently feasible for them to discover the weakness and figure out how to exploit it all on their own.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











