After being targeted by the Cl0p ransomware organization, the largest casino in Australia, Crown Resorts, revealed that there had been a data breach. The gang claims to have exploited a zero-day vulnerability (CVE-2023-0669) in Fortra’s GoAnywhere MFT secure file transfer product in order to steal sensitive data from over 130 different companies.
The campaign has targeted several businesses, including the largest casino in Australia. The data breach was discovered by the corporation only last week, but the event itself occurred in January.
Late in the month of January, an event took place in which a zero-day vulnerability in Fortra’s GoAnywhere managed file transfer (MFT) software was exploited in order to access data that belonged to Fortra clients.
The exploitation of the problem, which was tracked as CVE-2023-0669 and fixed at the beginning of February, was ascribed to a Russian-speaking threat actor connected with the Cl0p ransomware. The Cl0p ransomware has recently began uploading the identities of purported victims to its Tor-based leak site.
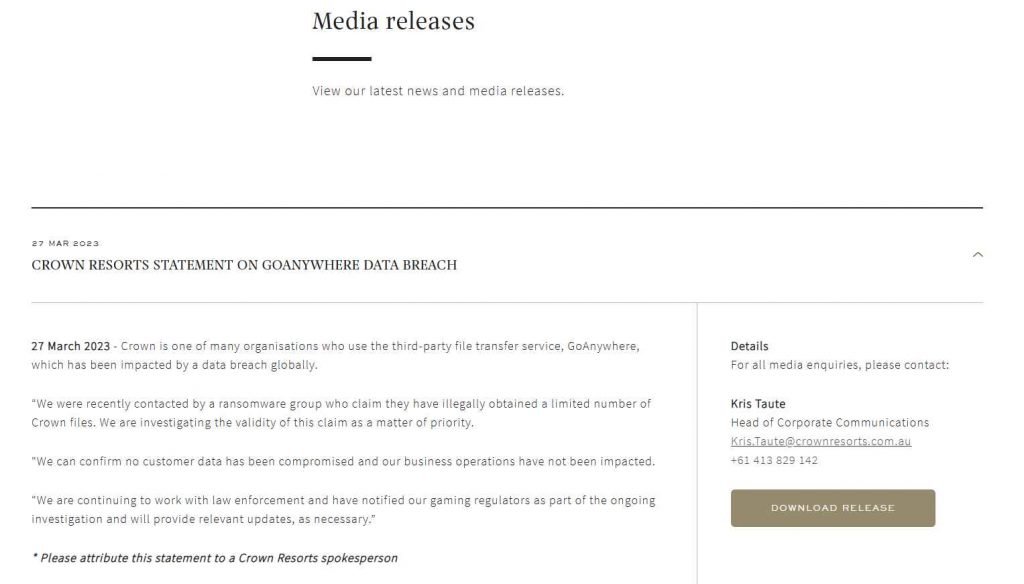
“Recently, we were approached by a ransomware gang that claims they have unlawfully stolen a select number of Crown data. As a matter of the highest importance, we are conducting an investigation into the veracity of this allegation. The statement that was issued by the corporation on March 27, 2023 may be read here. “We can affirm that none of our customers’ data has been compromised, and that there has been no effect on our company operations.” As part of the ongoing investigation, we are continuing to cooperate with law enforcement and have informed our gaming regulators. We will provide pertinent information as they become required.
Crown Resorts was just added to the list of victims that the Cl0p ransomware organization has released on its Tor leak site.
The operators of the Cl0p ransomware have claimed that their malware stole data from approximately 130 organizations that used GoAnywhere. A number of these organizations have already confirmed that they may have been affected by the attack. These organizations include Community Health Systems, Hitachi Energy, Hatch Bank, Rubrik, Atos, City of Toronto, Procter & Gamble, Pluralsight, Saks Fifth Avenue, UK’s PPF, Virgin Red, and Rio Tinto.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











