Check Point Research has been monitoring sophisticated attacks on authorities in numerous European countries since January 2023. The campaign made use of a broad number of tools, one of which was an implant, which is a tactic that is often linked with Chinese government-backed cybercriminals. This action has substantial infrastructure similarities with activities that have been previously published by Avast and ESET, which links it to the “Mustang Panda” malware family. This cluster of suspicious behavior is being monitored by CPR as “Camaro Dragon” at the moment.
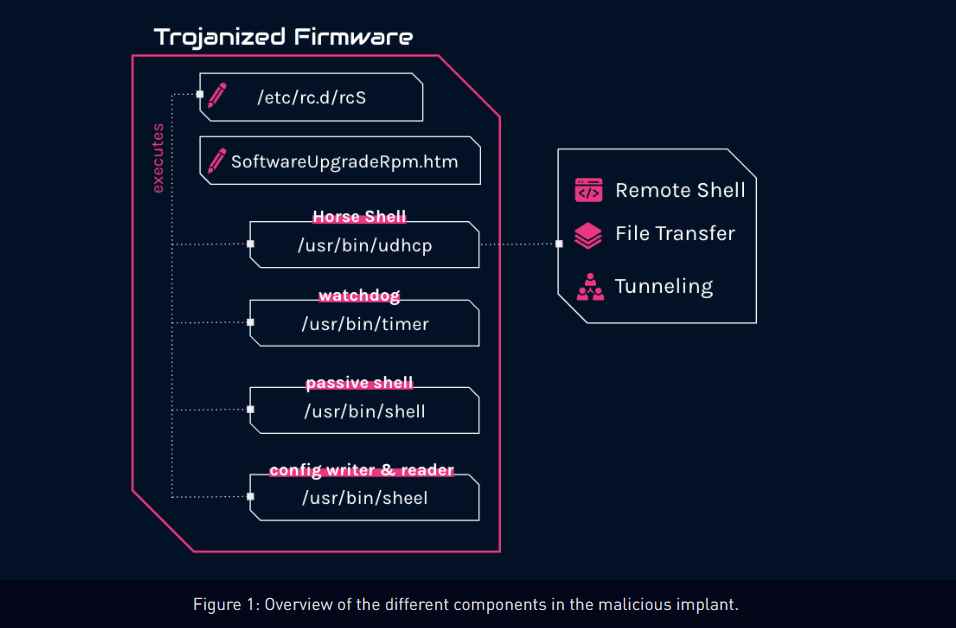
According to experts from Check Point named Itay Cohen and Radoslaw Madej, an investigation of these attacks has uncovered a bespoke firmware implant that was created specifically for TP-Link routers. “The implant features several malicious components, including a custom backdoor named ‘Horse Shell,’ that enables the attackers to maintain persistent access, build anonymous infrastructure, and enable lateral movement into compromised networks,” the firm claimed.
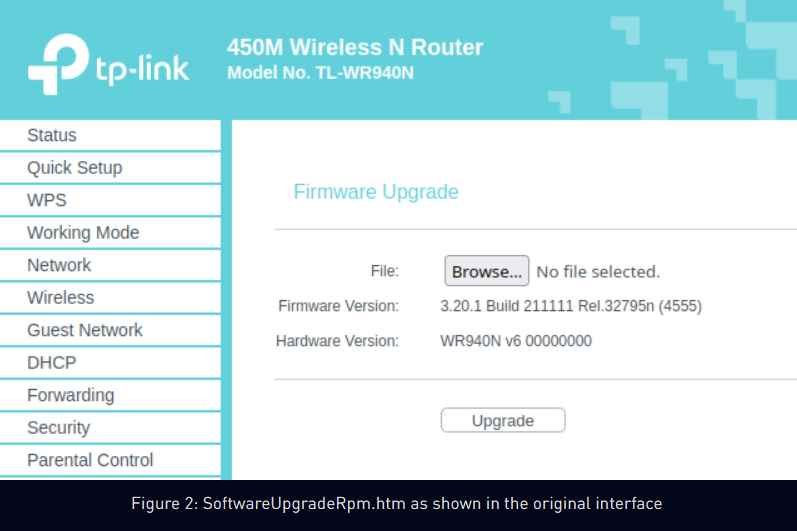
“Because of the implant’s firmware-agnostic design,” its components may be incorporated into different types of software by a variety of different manufacturers. At this time, the precise mechanism that was utilized to distribute the altered firmware images on the compromised routers is unclear. Likewise, its utilization and participation in real attacks are also unknown. It is believed that the first access may have been gained by taking advantage of security holes that were already known about or by brute-forcing devices that had passwords that were either the default or readily guessed.
According to what is currently known, the C++-based Horse Shell implant gives attackers the ability to run arbitrary shell commands, upload and download files to and from the router, and relay communication between two separate clients. However, in an intriguing turn of events, it is suspected that the router backdoor targets random devices on residential and home networks. This finding lends credence to the theory that hacked routers are being co-opted into a mesh network with the intention of establishing a “chain of nodes between main infections and real command-and-control.”
The purpose of relaying communications between infected routers by utilizing a SOCKS tunnel is to establish an extra layer of anonymity and disguise the end server. This is accomplished by the fact that each node in the chain possesses information only about the nodes that came before and after it in the chain.
To put it another way, the approaches obfuscate the origin and destination of the traffic in a manner that is comparable to how TOR works, which makes it far more difficult to discover the scope of the attack and disrupt it. The finding is just one more illustration of a long-standing pattern in which Chinese threat actors target internet-facing network equipment in order to manipulate the underlying software or firmware of such devices.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











