It has come to light that the Ninja Forms plugin for WordPress has many security flaws that might be abused by malicious actors to gain elevated access and steal sensitive data.
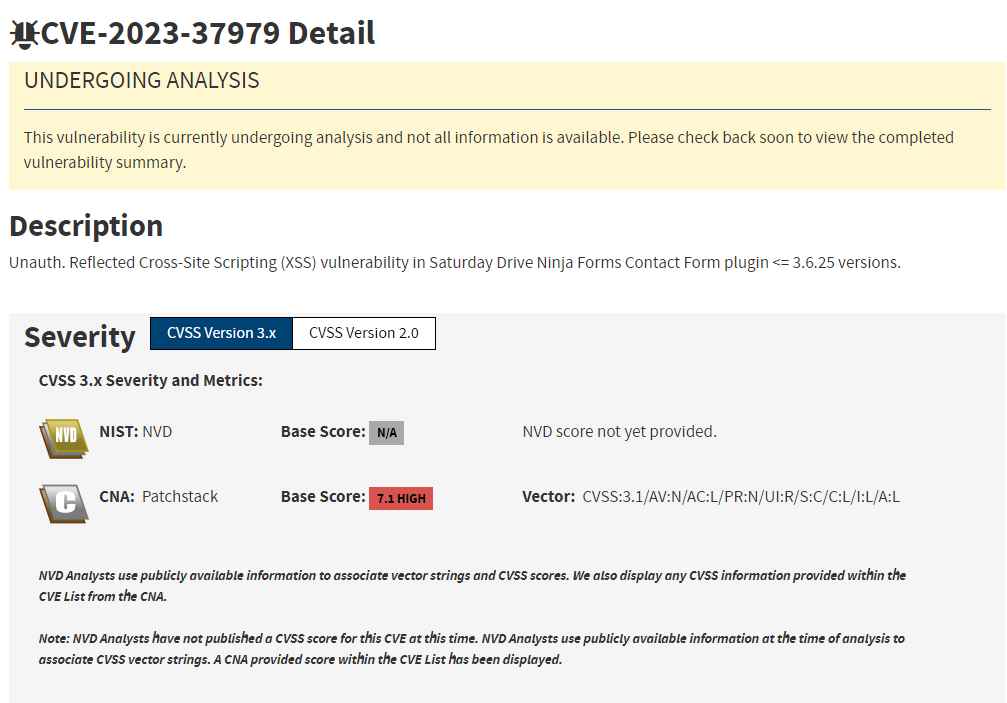
According to a report published by Patchstack a week ago, the vulnerabilities, which are listed as CVE-2023-37979, CVE-2023-38386, and CVE-2023-38393, affect versions 3.6.25 and earlier. There are now over 800,000 websites using Ninja Forms.
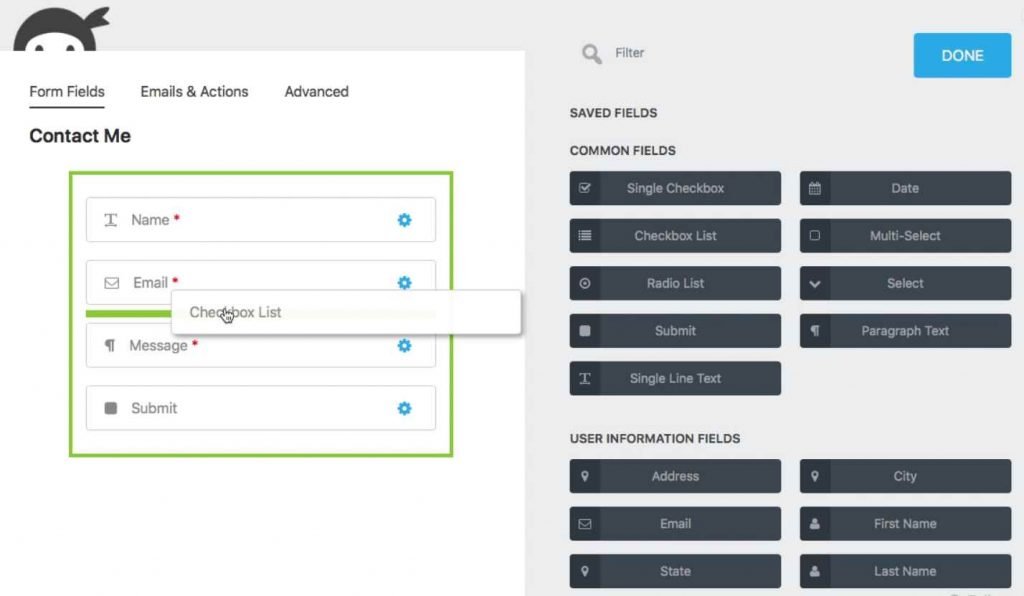
The following is a condensed explanation of each of the vulnerabilities:
CVE-2023-37979 is a POST-based reflected cross-site scripting (XSS) problem that has a CVSS score of 7.1. It is a vulnerability that might enable any unauthenticated user to accomplish privilege escalation on a target WordPress site by persuading privileged users to visit a website that has been specifically constructed for that purpose. This may be used by an unauthenticated user to their advantage to steal critical information and, in this instance, escalate their privileges on the WordPress website. The vulnerability may be triggered by the attacker if privileged users are tricked into visiting a specially constructed website.
The failed access control on form submissions export functionality is the source of the second and third vulnerabilities, which are tracked as CVE-2023-38393 and CVE-2023-38386 respectively. Users with the Subscriber and Contributor roles on a WordPress site may take advantage of the vulnerabilities to export all of the Ninja Forms submissions on the website.
Users of the plugin are strongly encouraged to upgrade to version 3.6.26 in order to protect themselves against any possible dangers.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











