The benefits of joining a particular club over others are highlighted in travel rewards programs like those run by airlines and hotels. The digital architecture of a number of these programs, including as Delta SkyMiles, United MileagePlus, Hilton Honors, and Marriott Bonvoy, is, however, based on the same platform behind the scenes. The backend was developed by Points, a firm that specializes in loyalty commerce and offers a suite of services, one of which is an extensive application programming interface (API). Between the months of March and May of 2023, reports of points.com containing security flaws were received.This information on the vulnerabilities in the Points.com API was made public by a group of cybersecurity experts on August 3, 2023, along with the technical particulars of their attack.

Attackers would have access to sensitive customer account information, the ability to transfer points from customer accounts, and obtain unauthorized access to a worldwide administrator website using these stated vulnerabilities.Points.com is the company that handles the warehousing and processing of reward points for the vast majority of the major hotel and airline loyalty programs.
Between the months of March and May, the researchers, who went under the names Ian Carroll, Shubham Shah, and Sam Curry, disclosed a number of vulnerabilities to Points.com, and since then, all of the problems have been addressed.
An unauthenticated HTTP call to an internal API was the initial vulnerability that they discovered and reported on March 7, 2023. If an attacker had exploited this flaw, they would have been able to query 22 million customer orders.”The data contained within the records included partial credit card numbers, home addresses, email addresses, phone numbers, reward point numbers, customer authorization tokens, and various transaction details,” said Sam Curry, a researcher in the field of cybersecurity. “The data also included miscellaneous transaction details.”
The permission bypass was the second vulnerability that they discovered and disclosed on March 7, 2023.
Information Regarding Customers’ Private Lives Made Public
Through the misuse of an application programming interface (API), it would be possible for an adversary to steal airline reward points from other customers by knowing just their last name and reward points number.
The third vulnerability that they disclosed on May 2, 2023 was a Leaked Tenant Credentials issue on an endpoint that was hosted by the Virgin Rewards Program. This vulnerability gives attackers the ability to Sign API Requests on Behalf of Virgin Airways (Add/Remove Rewards Points, Access Customer Accounts, Modify Rewards Program Settings, etc.). This vulnerability was discovered on an endpoint that was hosted by the Virgin Rewards Program.
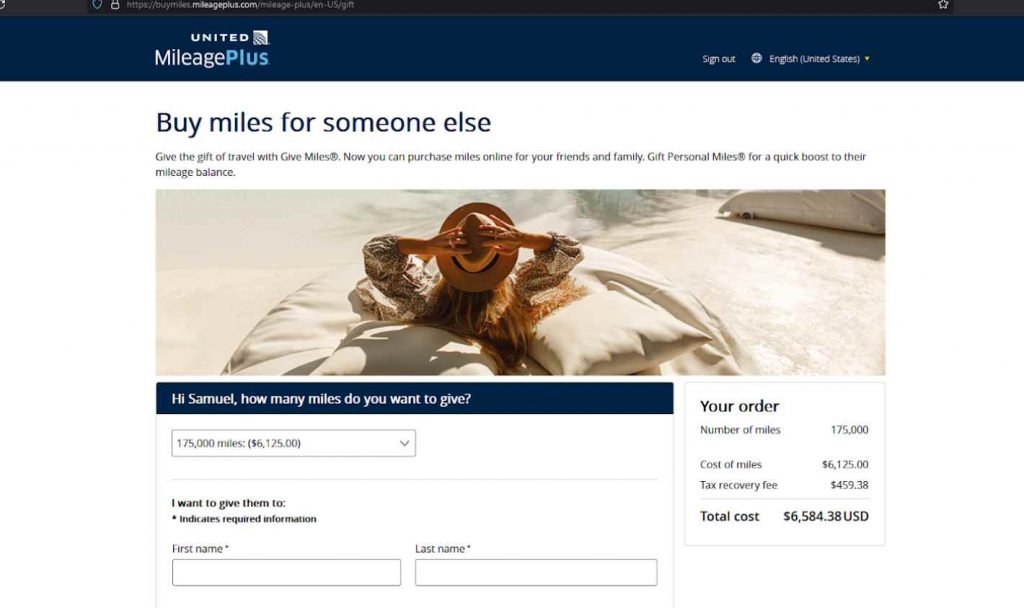
On April 29, 2023, they discovered the fourth vulnerability, which was present in United Airlines particularly. This flaw allowed an attacker to produce an authorization token for any user by only knowing the user’s rewards number and last name.
An authorization token might be provided by the attacker.
Because to this vulnerability, an attacker could be able to execute actions such as transferring miles to themself and authenticating as a member on several MileagePlus-related applications, which might even include the MileagePlus administrator panel.The most recent vulnerability they discovered was on May 2, 2023, and it allowed an attacker to acquire complete access to the administration interface of globalpoints.com as well as the administration panel of the loyalty wallet.
This access might be abused by an adversary to revoke already established reward program credentials and temporarily disable airline rewards functionality.
The points.com staff acknowledged every issue within an hour of receiving them, which demonstrates how promptly they reacted after being informed of the vulnerabilities.
They immediately pulled the impacted websites down in order to perform in-depth examinations, and thereafter they fixed all of the flaws that were discovered. According to the Sam Curry team, “all of the vulnerabilities that were reported have since been remediated.”

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











