A new sextortion scam is doing the rounds that impersonates an email from the pornographic website YouPorn and warns that a sexually explicit video of the victim has been published to the website while also requesting that the victim pay money to get the video removed from the website.
Sextortion email scams include the con artists pretending to have photographs or films of the victim engaging in sexual behaviors and then demanding financial compensation so that the material is not made public.
In comparison to mail from fictitious hackers secretly recording compromising videos or law enforcement issuing fines, threatening legal action/charges for viewing/possession of illegal pornographic material, spam emails like “YouPorn,” or those claiming that explicit content depicting the recipient has been uploaded to legitimate platforms, are relatively new.
Infectious files may be included to spam campaigns or linked to as downloads from inside the messages themselves. Documents (such as PDF, Microsoft Office, Microsoft OneNote, and so on), executables (such as.exe and.run), archives (such as ZIP and RAR), JavaScript, and so on are all examples of the types of files that fall under this category. When a file of this kind is accessed, infection chains are set into motion.
Following an investigation, we have concluded that the “YouPorn” email in question is fraudulent. There are a few distinct variations of this spam email, but they are all essentially a new take on the sextortion fraud.
A sexually explicit video or image may have been recently released on the YouPorn website, and the sender may have falsely claimed that the receiver may be recognized in the video or image. The emails offer a number of payment alternatives for removing the content and preventing it from being reuploaded in the future.
It is imperative that it be brought to everyone’s attention that all of the assertions made by these letters are completely fictitious, and that this mail is in no way affiliated with the genuine YouPorn website.
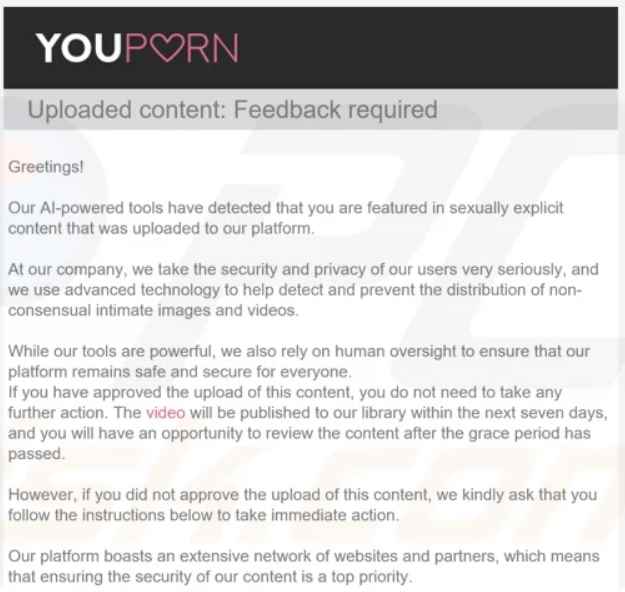
It notifies the receiver that YouPorn’s AI-powered algorithms have discovered that they have been featured in video that contains sexually explicit content. This is a precautionary safety step since it is against the regulations of YouPorn to distribute recordings or pictures of anyone engaging in sexual activity without their consent.
If the receiver gave permission for the material to be posted on the platform, the recipient does not have to take any more action. The material will be made accessible for the recipient’s approval as well as the review of other users of the website after a waiting period of seven days.
In the event that this does not occur, the letter provides a variety of alternative removal strategies. There are a few variations of the “YouPorn” email scam that promise free uninstallation; however, when the receiver tries to pick this option, they are sent back to the homepage of their browser since the URL provided is empty. Because of this, victims are compelled to investigate the many payment-related choices, which are presented in the various versions of the email.
The one that we looked at included an option that cost $199 and included “basic express removal, blocking, and protection against re-uploading” for twenty different websites that were part of YouPorn’s partner network. The option “Plan A,” which costs $699 and offers protection for one full year as well as an increase in the number of protected sites to 300, also extends the coverage period. Although “Plan B” costs $1399, it is a three-year option that includes “Plan A” and adds face recognition techniques to make it easier to block inappropriate information. Additionally, “Plan A” is included in “Plan B.”
Since the transaction is fully automated, there is no need for the receiver to participate in any way, since the only kind of money that can be used to make the payments is Bitcoin.
All of the assertions that are made in these spam emails are not true, as was stated earlier. In addition, YouPorn and any other genuine businesses or companies are in no way connected to this phishing email in any way, shape, or form. As a consequence, the receivers of these messages are not in any genuine danger.
The victims of this fraud suffer financial losses, and they are unable to recover their money since bitcoin transactions are very impossible to track.
Because spam email is so pervasive and can be so professionally crafted, we highly urge exercising extreme care with receiving emails, private messages and direct messages, text messages, and other types of messaging. It is important to remember not to click any links or attachments that come with suspicious emails since they can contain malware.
We strongly suggest using a version of Microsoft Office that was released after 2010, since these versions provide a “Protected View” option that stops automatic macro execution.
Because malicious software is not only spread via unsolicited email, following our advice to download only from legitimate and reliable sources is strongly recommended.
It is also recommended that software be activated and updated by using the features and tools made available by the official creators of the software. This is due to the fact that tools used for unlawful activation (also known as “cracking”) and updates given by third parties may include malware.
In addition, since there is a large quantity of false and hazardous stuff on the Internet that is well disguised, it is imperative to exercise extreme caution while one is surfing the web.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











