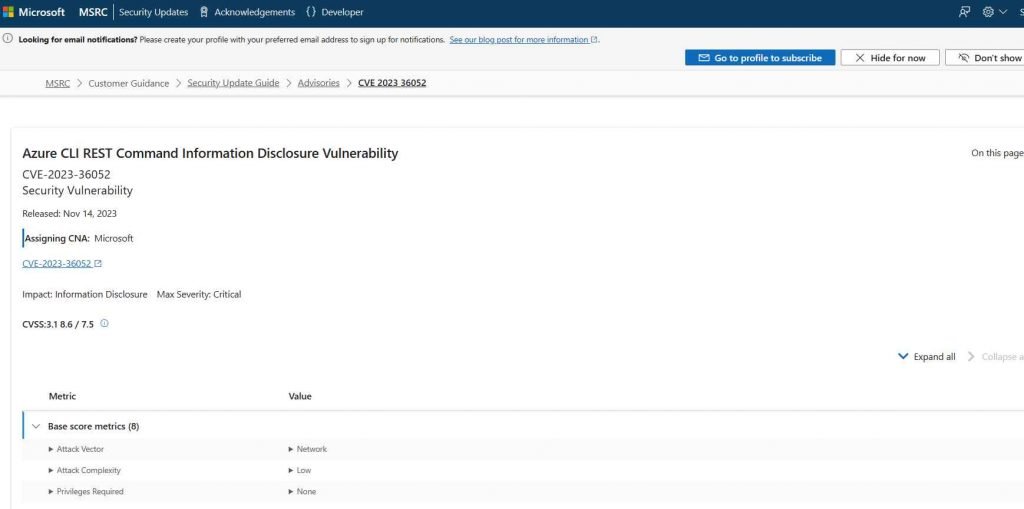
CVE-2023-36052 is a critical security vulnerability in the Azure Command-Line Interface (CLI), a tool for managing Azure resources. This vulnerability, reported by Palo Alto’s Prisma Cloud, allowed unauthenticated attackers to remotely access plaintext contents, including usernames and passwords, from Continuous Integration and Continuous Deployment (CI/CD) logs created using Azure CLI. These logs could be published by Azure DevOps and/or GitHub Actions. To mitigate this risk, users were advised to update their Azure CLI to version 2.53.1 or above.
Let’s consider a hypothetical example to understand the implications of CVE-2023-36052:
Suppose a development team uses Azure CLI for managing their Azure resources and automates their deployment process using GitHub Actions. During their routine operations, they execute various Azure CLI commands which generate logs. These logs, by default, include plaintext credentials such as usernames and passwords.
An external attacker, aware of this vulnerability, could access the public repository where the team’s GitHub Actions are configured. By examining the CI/CD logs published there, the attacker could find and extract these plaintext credentials. With these credentials, the attacker could gain unauthorized access to the team’s Azure resources, potentially leading to data breaches, unauthorized modifications, or even service disruptions.
This scenario underscores the critical nature of CVE-2023-36052, where seemingly benign logs could inadvertently become a source of significant security breaches. The mitigation steps provided by Microsoft, including updating Azure CLI and implementing best practices for log management and key rotations, are essential to prevent such unauthorized access.
Mitigation
Microsoft implemented several measures to address this vulnerability. These include:
- Azure CLI Update: Advising customers to update Azure CLI to the latest release.
- Securing Logs: Avoiding exposure of Azure CLI output in logs or publicly accessible locations and implementing guidance for masking environment variables.
- Regularly Rotating Keys and Secrets: Encouraging regular rotation of keys and secrets.
- Reviewing Security Best Practices: Providing guidance on secrets management for Azure services and GitHub Actions, and ensuring GitHub repositories are private unless necessary to be public.
- Securing Azure Pipelines: Offering guidance for securing Azure Pipelines.
- Enhancing Default Configurations: Introducing a new default configuration in Azure CLI to prevent accidental disclosure of sensitive information. This included restricting the presentation of secrets in output from update commands and broadening credential redaction capabilities across GitHub Actions and Azure Pipelines.
Workaround
Without patching, the primary alternative way to mitigate the risks associated with CVE-2023-36052 involves several best practices and security measures:
- Secure Logging Practices: Ensure that logs do not contain sensitive information. This might involve custom scripts or tools to filter out or obfuscate credentials and other sensitive data before they are logged.
- Access Control on Logs: Restrict access to CI/CD logs. Ensure that only authorized personnel can view these logs, and they are not publicly accessible.
- Frequent Credential Rotation: Regularly change credentials and secrets to reduce the window of opportunity for an attacker to use compromised credentials.
- Monitoring and Alerting: Implement monitoring to detect unusual access patterns or usage of credentials, which might indicate a compromise.
- Environment Segmentation: Segregate development, testing, and production environments. Limit the scope of what each environment can access to minimize potential damage.
However, these measures are more complex and potentially less effective than updating the Azure CLI to a patched version. Patching directly addresses the vulnerability at its source, providing a more comprehensive and straightforward solution.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











