In a case that redefines the boundaries of modern cybercrime, a threat actor known as UNC2891 has carried out a multi-vector cyber-heist targeting ATM infrastructure across several banking institutions. Group-IB’s threat intelligence reveals a campaign that combines physical infiltration, low-level Linux malware, and sophisticated forensic evasion techniques, culminating in attempted manipulation of ATM switch systems and HSM (Hardware Security Module) spoofing.
UNC2891 bypassed traditional endpoint security and network monitoring by exploiting weaknesses in bootloader integrity, leveraging bind mount-based rootkit evasion, and controlling pivot infrastructure through covert backdoors.
Who Is UNC2891?
UNC2891 is an advanced threat group suspected to operate with deep knowledge of banking infrastructure, particularly Linux-based ATM systems and payment switch architecture. The campaign shows clear hallmarks of state-level sophistication but remains financially motivated. Their ability to exploit both physical and digital infrastructure in tandem is notable — especially given the group’s stealth and lateral movement capabilities.
Technical Anatomy of the Attack
Physical Access & Bootloader Hijack
Attackers physically accessed the ATM’s internals and injected a custom GRUB2 bootloader using a USB device, booting a modified Linux image.
menuentry 'Recovery' {
set root=(hd0,1)
linux /vmlinuz root=/dev/sda1 init=/malware/init quiet
initrd /initrd.img
}
This bypassed Secure Boot (when disabled), allowing full kernel control.
Memory-Resident ATM Malware
Using LD_PRELOAD techniques and shared object injection, UNC2891 hijacked ATM processes without modifying them on disk.
int dispense_cash() {
if (getenv("TRIGGER") != NULL) {
run_command("dispense --amount=1000");
}
return original_dispense();
}
Privilege Escalation & Rootkit Deployment
The threat actor deployed Loadable Kernel Modules (LKMs) to hook system calls and hide their processes, files, and network traffic.
Persistence & Anti-Forensics
Persistence was achieved via custom systemd services and GRUB modifications, while forensic tools were neutralized via:
- Hijacked
ps,netstat, andlsbinaries - Custom logging suppressors
- Execution in memory using tmpfs
- Masquerading binaries as known system processes
Network Forensics Exposed Hidden Beaconing
Despite its stealth, the operation left behind subtle indicators. A review of the Network Monitoring Server’s traffic revealed periodic beaconing every 600 seconds to a Raspberry Pi device on port 929. Strangely, no active process was linked to these connections during triage — a strong sign of rootkit-level evasion.
This sparked questions about whether typical forensic tools capture process states during sleep or idle, prompting investigators to deploy a custom socket-capture script that ran every second for 10 minutes.
The script confirmed: connections were occurring — but no standard tool could attribute them to a PID.
Masquerading of the Backdoor Process
During memory analysis, two suspicious processes were found:
lightdm --session 11 19
They mimicked legitimate lightdm display manager processes — but their locations were suspicious:
/tmp/lightdm (PID 8239)
/var/snap/.snapd/lightdm (PID 8914)
The attacker used process masquerading to evade detection. The binary lightdm appeared legitimate, but the execution path and arguments were fabricated to fool incident responders.
These backdoors maintained active connections to:
- The Raspberry Pi (on-site covert access)
- The internal Mail Server (used as a persistent C2 relay)
Why Triage Tools Missed It
The forensic blind spot stemmed from UNC2891’s use of Linux bind mounts to hide the true /proc/[pid] paths — an evasion method not previously documented in public threat reports.
For example:
tmpfs on /proc/8239 type tmpfs (rw,nosuid,nodev)
ext4 on /proc/8914 type ext4 (rw,relatime,...)
This redirected forensic tools away from the real process details, completely masking the backdoor’s presence. The technique has since been codified under MITRE ATT&CK T1564.013 – Hide Artifacts: Bind Mounts.
UNC2891’s Ultimate Objective: ATM Switch Takeover
Group-IB’s analysis determined the attacker was moving laterally toward the ATM switching server, intending to deploy a custom rootkit called CAKETAP. This malware is designed to:
- Intercept HSM communication
- Spoof transaction authorization messages
- Facilitate unauthorized ATM cash-out via fake approvals
Although the campaign was interrupted before success, its complexity highlights serious exposure in financial infrastructure.
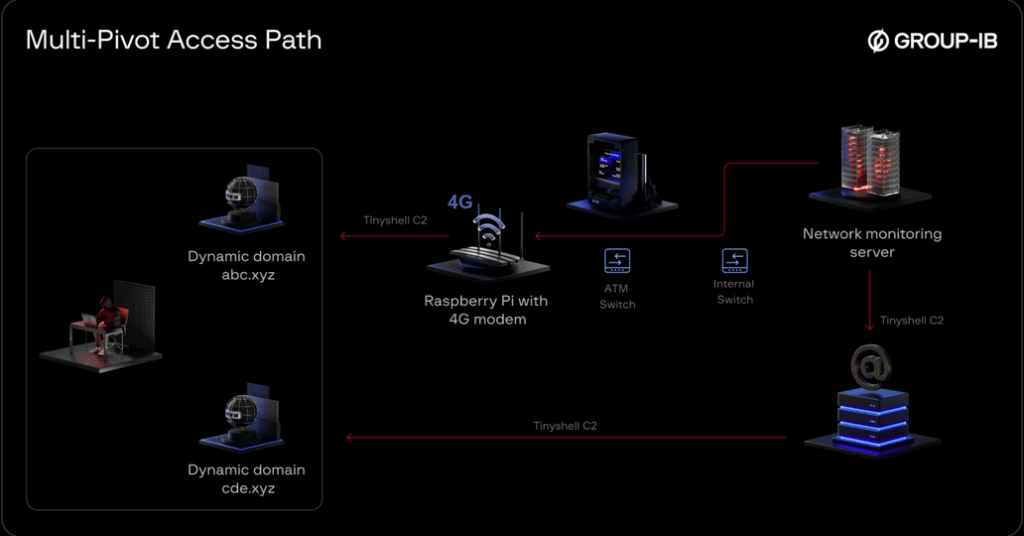
Incident Summary & Multi-Pivot Access
UNC2891 orchestrated a multi-pivot attack combining:
- Physical access via ATMs
- Lateral movement through the Network Monitoring Server
- Persistence via the internal Mail Server (which had external connectivity)
Additional C2 obfuscation included use of Dynamic DNS, allowing:
- Rapid IP rotation
- Infrastructure replacement
- Harder attribution and disruption
Detection & Defense Recommendations
To defend against attacks like this:
Linux EDR/Forensics
- Monitor
mountandumountsyscalls (viaauditd,eBPF, etc.) - Alert on
/proc/[pid]mounted totmpfsor strange filesystems - Block execution of binaries from
/tmp,.snapd, or mounted USBs
Network & Infrastructure
- Segment ATM network from monitoring infrastructure
- Monitor for beaconing to unknown local IPs or odd ports (e.g., 929)
- Physically secure ATM-connected ports and block unauthorized USB devices
Incident Response
- Always collect memory dumps in addition to disk images
- Use custom scripts to capture real-time socket/PID associations
- Treat system processes outside expected paths as suspicious (
lightdm,sshd, etc.)
UNC2891’s attack demonstrates that cybercriminals are increasingly blending physical access, kernel-level malware, and advanced anti-forensics to stay undetected — even in highly regulated industries like banking.
Traditional detection methods failed not due to a lack of tooling, but because the attackers operated below the radar — in memory, in hardware, and outside the expected process trees.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











