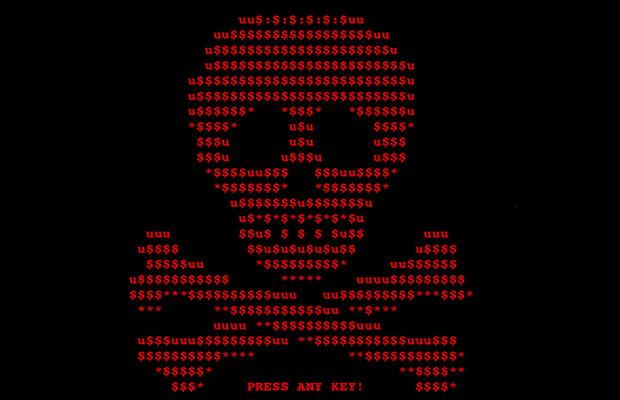
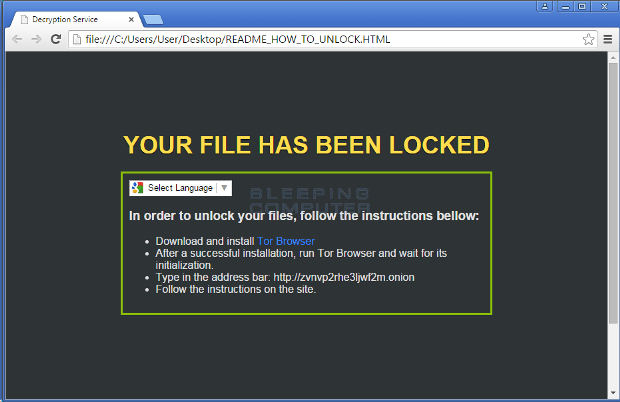
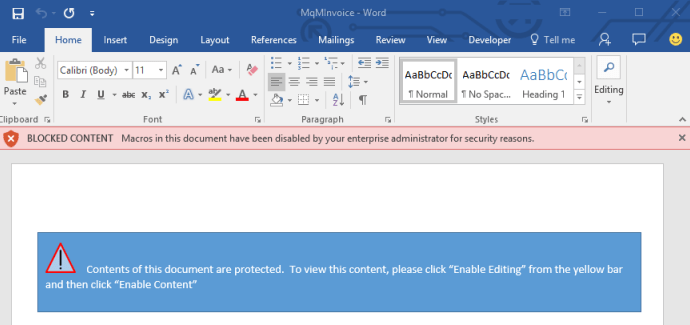
Petya Ransomware’s Encryption Defeated and Password Generator Released
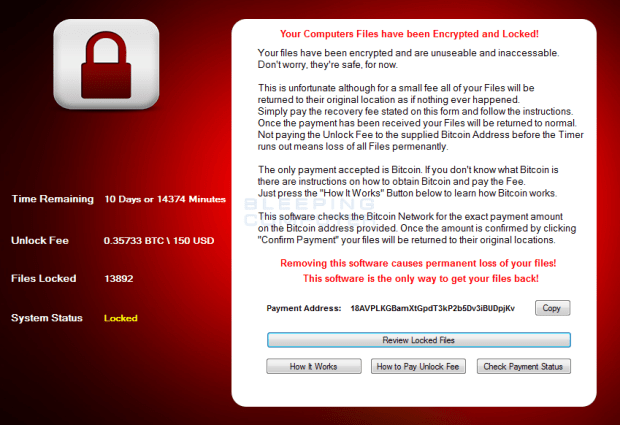
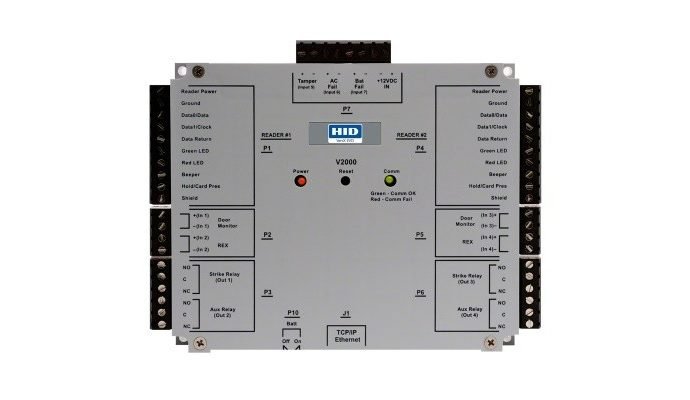
An individual going by the twitter handle leostone was able to create an algorithm that can generate the password used to decrypt a Petya encrypted computer. In my test this, this algorithm was ableRead More →