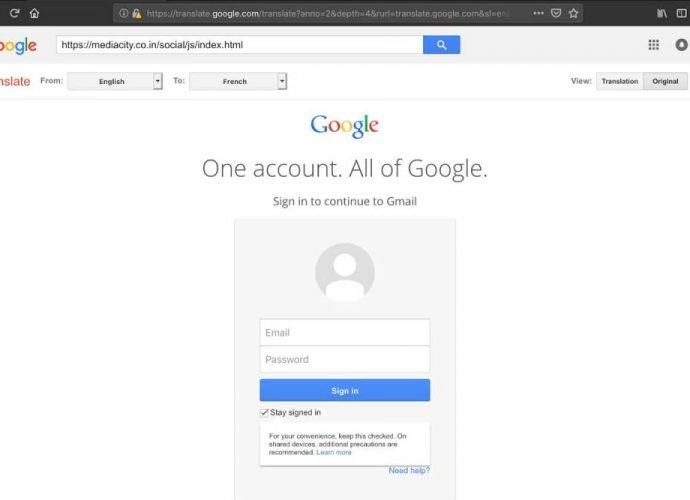
Criminals in darknet seek to recruit business employees: How to Prevent
Organizations face a new inside threat Cybercriminals have rendered the darknet into their workplace. According to security monitoring and ethical hacking experts from the International Institute of Cyber Security, inRead More →