A security report mentions that two hospitals in New York City have been the victims of a ransomware incident that disrupted some of their regular operations. Canton-Potsdam, Massena and Gouverneur executives have already confirmed the incident, mentioning that personal patient and employee information has not been compromised. This is a serious incident considering that the world remains in the fight against coronavirus, so hospitals are considered critical infrastructure.
“As a security measure, all affected systems were disconnected to prevent further spread of infection; patient care continues to be provided safely and effectively,” says a joint statement. Still, the unforeseen event of the incident has caused many of the hospital’s regular activities (shift changes, patient records, and prescriptions) to be carried out with pencil and paper.
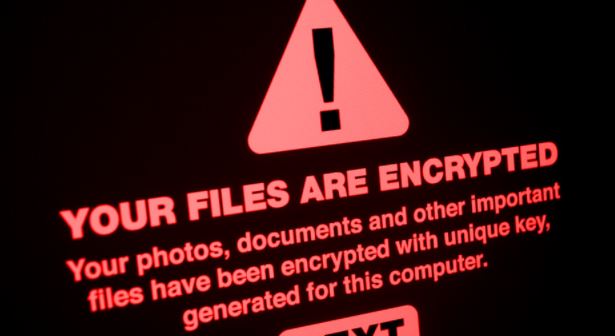
As many remember, ransomware is a cyberattack variant that infects computers, blocks access to a device and demands a ransom from victims in exchange for restoring their systems to normal. In this case, threat actors used the Ryuk ransomware variant, widely popular among hacker groups.
Officials at the affected hospitals have notified the Federal Bureau of Investigation (FBI) and the Department of Homeland Security (DHS): “We implement appropriate controls to prevent similar incidents from coming forward and will continue to work to restore our systems as soon as possible,” concludes the statement.
On the other hand, the New York State Department of Health confirmed the cyberattack against these health centers: “The DOH has been in communication with St. Lawrence Hospital System, which operates Canton-Potsdam Hospital and Gouverneur Hospital, on a cyberattack,” said Jeffrey Hammond, DOH representative.
The affected county emergency response team also mentioned that facilities affected by ambulance delivery were supported on Tuesday morning, so patients requiring critical attention will not be affected by this incident.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











