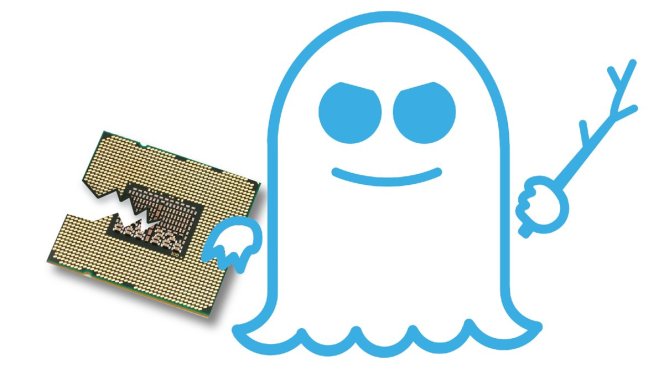
SgxSpectre Exploits Recent Intel CPU Flaw And Leaks “Enclave” Secrets
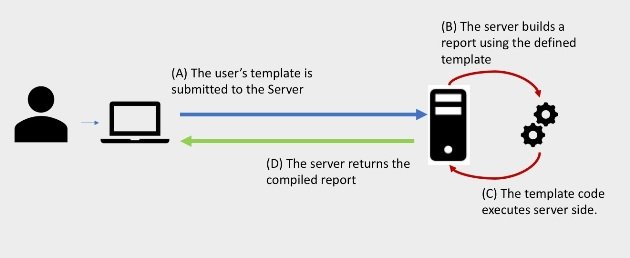
In modern Intel processors, there’s a hardware extension available named Software Guard Extension (SGX) to improve the security aspects. It provides a shielded execution environment called ‘enclaves’ to deal withRead More →