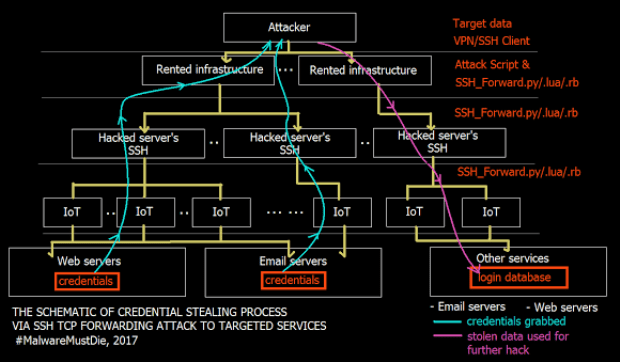
Exclusive: A criminal group using SSH TCP direct forward attack is also targeting Italian infrastructure
Exclusive: MalwareMustDie for Security Affairs released the list of the sites under attack. A criminal gang is using SSH TCP direct forward attack technique. MalwareMustDie is back and has published his theRead More →