ImageTragick Exploit Used in Attacks to Compromise Sites via ImageMagick 0-Day
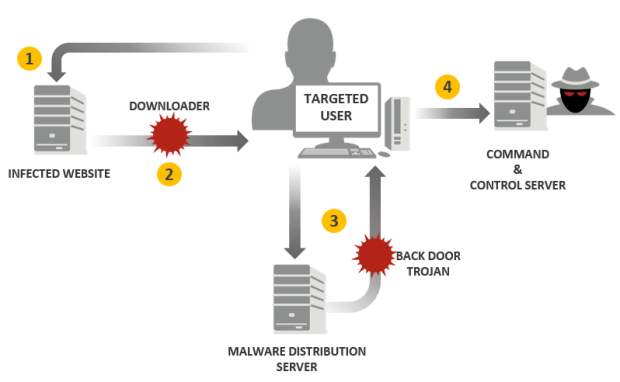
imageMagick project hopes to publish a patch today. Two Russian security researchers revealed a few hours ago a vulnerability in the ImageMagick image processing library deployed with countless Web servers, aRead More →