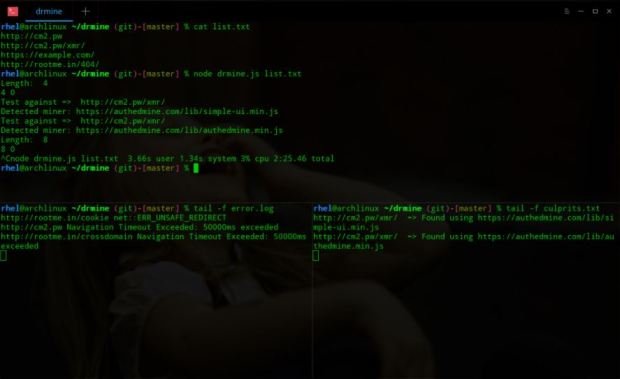
Dr. Mine a tool that allows us to know if a web is mining cryptocurrency
Dr. Mine is a script programmed in NodeJS designed specially to help the detection of the cryptocurrency mining in the different webs that we are going to visit. According to cyberRead More →