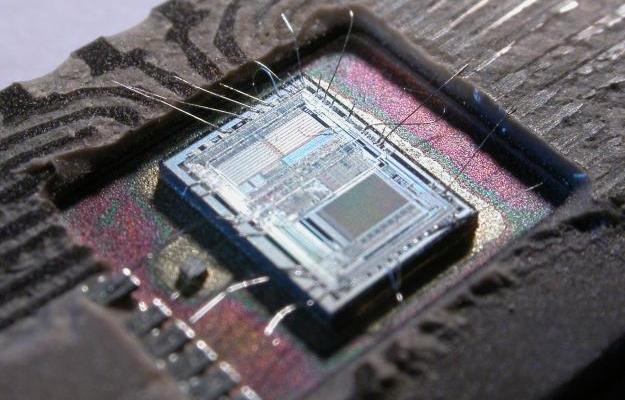
Experts can hack most CPUs since 2008 over USB by triggering Intel Management Engine flaw
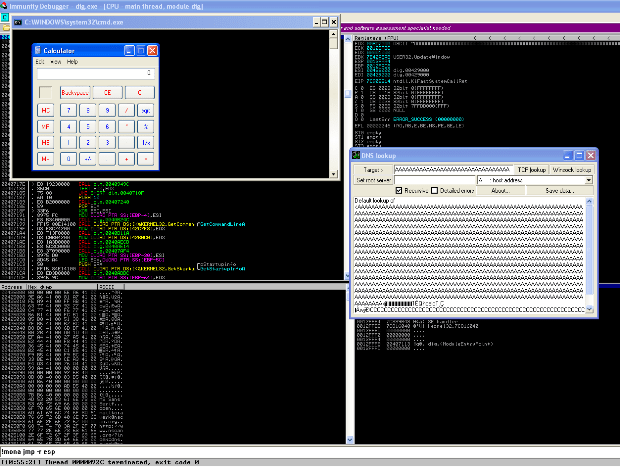
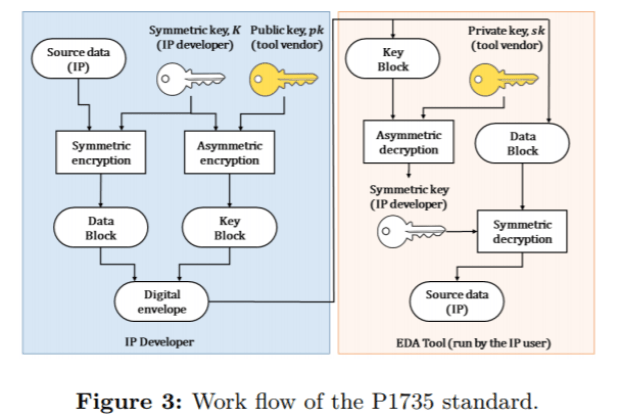
Intel’s management engine – in most Positive Technologies plans to demonstrate at the next Black Hat conference how to hack over USB into Intel Management Engine of most CPUs sinceRead More →