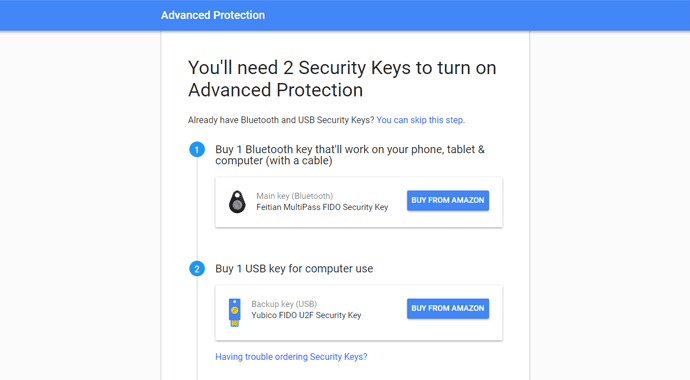
Google introduces new Advanced Protection feature to protect its users
Google continues working to improve the security of its users, the last measure introduced by the company it the ‘Advanced Protection’ feature. The Advanced Protection feature was designed to improve theRead More →