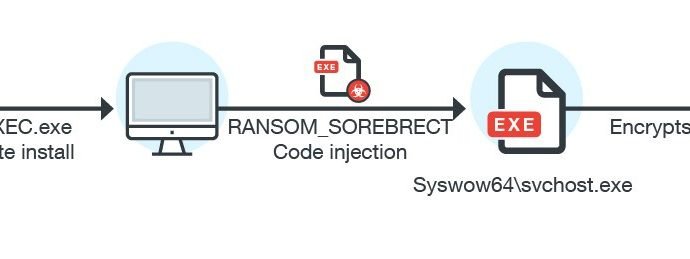
New Code-injecting SOREBRECT Fileless Ransomware detected in the wild
The number of fileless malware continues to increase, recently security researchers spotted a new Fileless Ransomware dubbed Sorebrect. Sorebrect is able to inject malicious code into a legitimate system process (svchost.exe) onRead More →