A Dissection of the “EsteemAudit” Windows Remote Desktop Exploit
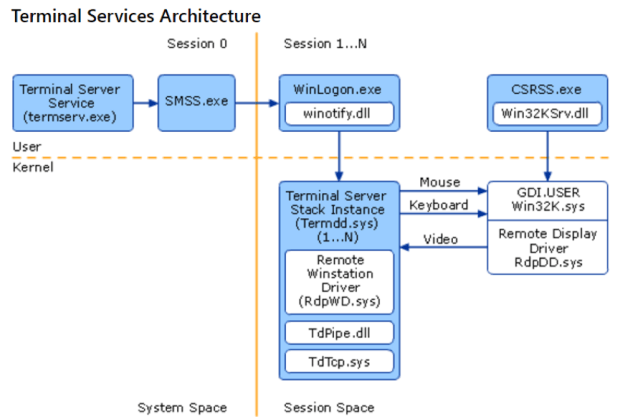
In April, a group known as the “Shadow Brokers” released a cache of stolen information that included multiple tools to exploit vulnerabilities in various versions of Microsoft Windows. The mostRead More →