Stolen Passwords Fuel Cardless ATM Fraud
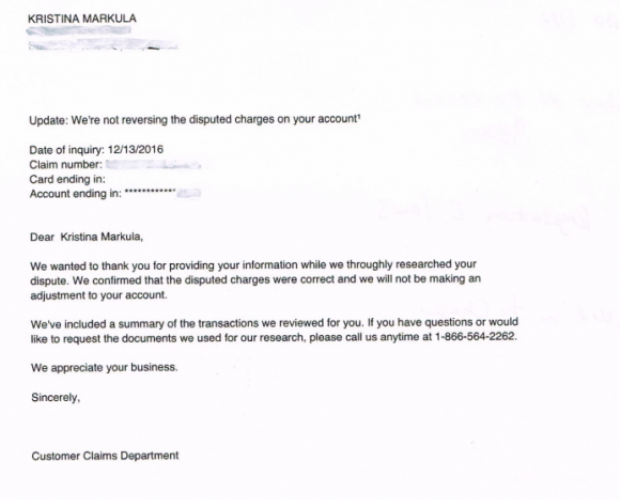
Some financial institutions are now offering so-called “cardless ATM” transactions that allow customers to withdraw cash using nothing more than their mobile phones. But as the following story illustrates, this new technologyRead More →