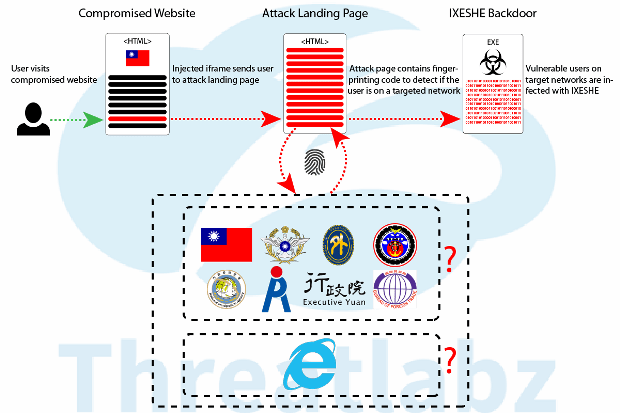
CNACOM – Open Source Exploitation via Strategic Web Compromise
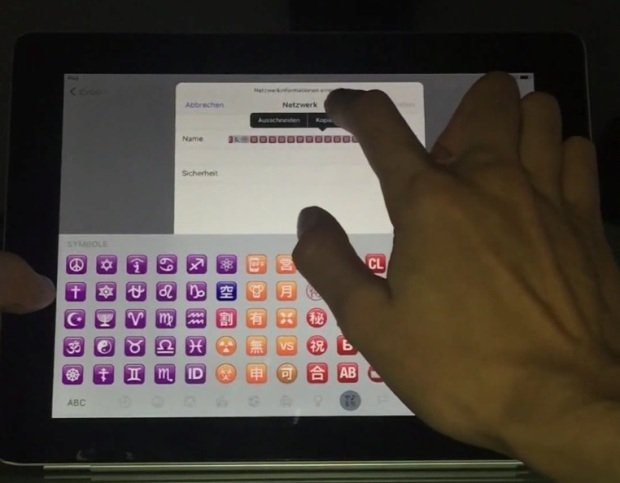
Since a full proof of concept for CVE-2016-0189 vulnerability was published on GitHub, Zscaler ThreatLabZ has been closely tracking its proliferation. The first copying of the exploit code we spottedRead More →