How to compromise PLC systems via stealthy Pin control attacks
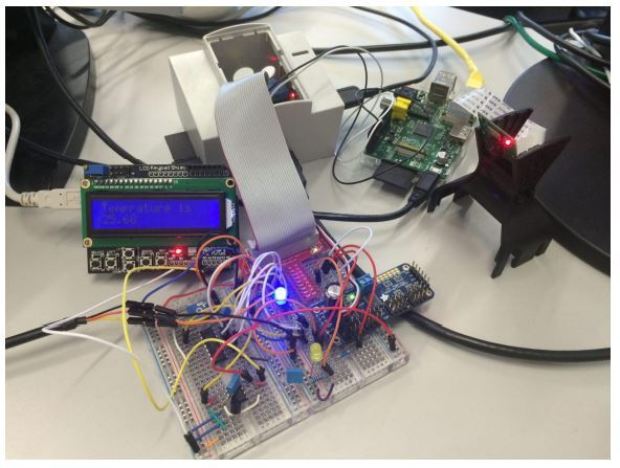
At the Black Hat Europe 2016 two security researchers devised undetectable attacks that could be used to hack PLC systems avoid being detected. Security researchers at the Black Hat EuropeRead More →