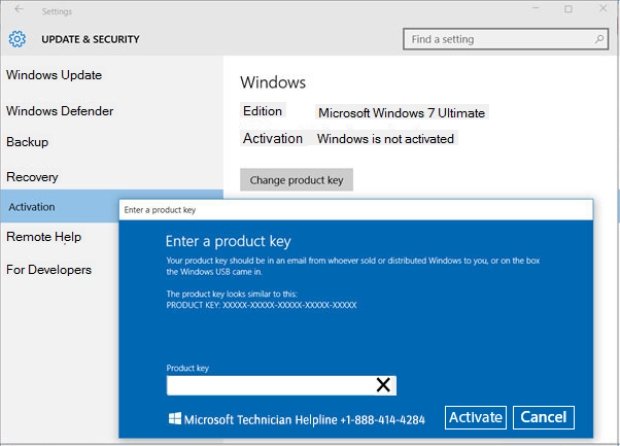
With the looming threat of Ransomware, should companies stockpile Bitcoins?
With the threat of ransomware hanging over every company’s head, does it make sense for companies to stockpile a few bitcoins in the event of a ransomware attack? Yeah, yeah, IRead More →