Intel x86 CPUs Come with a Secret Backdoor That Nobody Can Touch or Disable
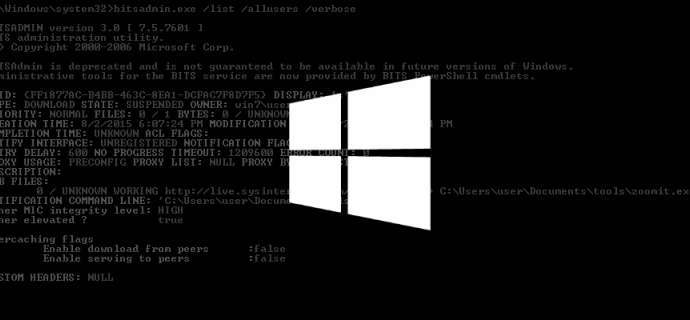
Intel x86 CPUs Come with a Secret Backdoor That Nobody Can Touch or Disable. Hardware security expert Damien Zammit says that recent Intel x86 CPUs come with a secret subsystemRead More →