How to define information security plan?
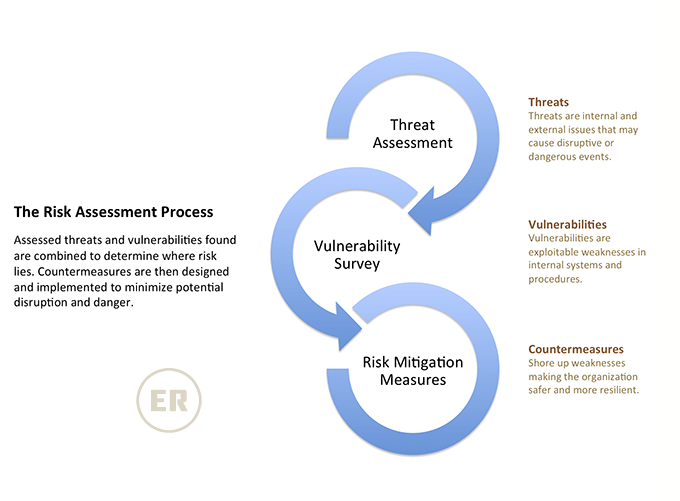
The information security plan describes how the security is implemented, defined policies, controls and solutions. The information security plan is developed considering all the IT resources depending on the securityRead More →