Decrypted: Kaspersky releases free decryptor for CryptXXX Ransomware
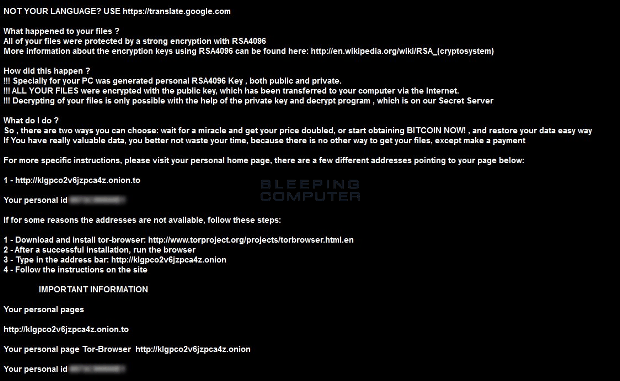
Last week Kafeine posted an analysis of a new ransomware called CryptXXX on the Proofpoint blog. Based on their analysis they determined that CryptXXX is affiliated with the developers of theRead More →