Hearthstone add-ons, cheating tools come with data-stealing malware
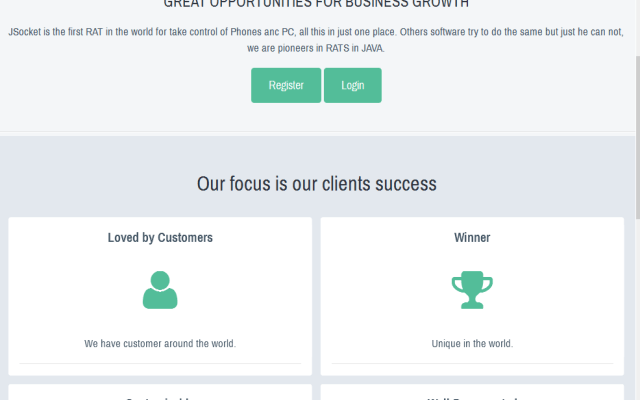
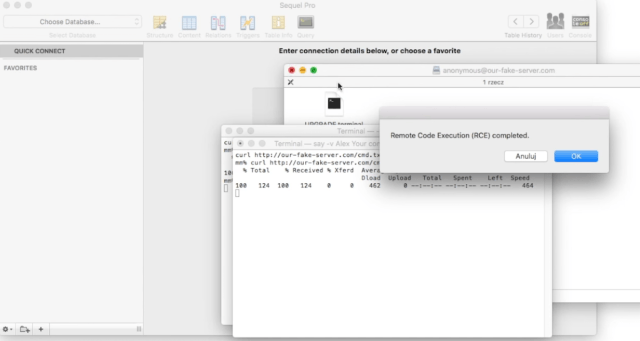
Attackers have disguised information-stealing and Bitcoin malware as third-party add-ons and cheats for Blizzard’s online card game. Hearthstone, a free-to-play card game based on World of Warcraft, has been indirectlyRead More →