How to Hack the Power Grid Through Home Air Conditioners
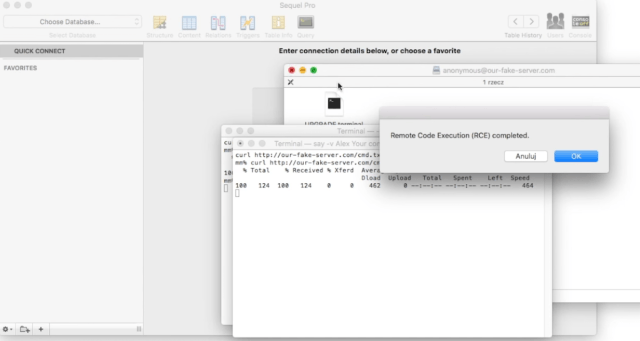
TENERIFE, SPAIN—THERE ARE many ways we know of to cause a blackout. You could hack industrial equipment to spin a generator out of control. You couldhijack operator machines and remotelyRead More →