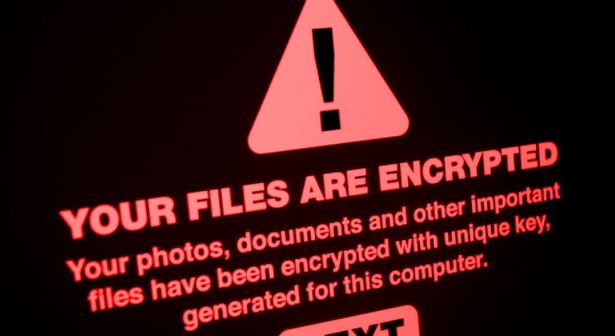
Critical vulnerabilities in NGINX allows complete takeover of affected systems. Exploit publicly available; patch now
Nginx security teams published a report related to a critical vulnerability in their DNS resolution implementation. Tracked as CVE-2021-23017, successful exploitation of this vulnerability would allow threat actors to takeRead More →