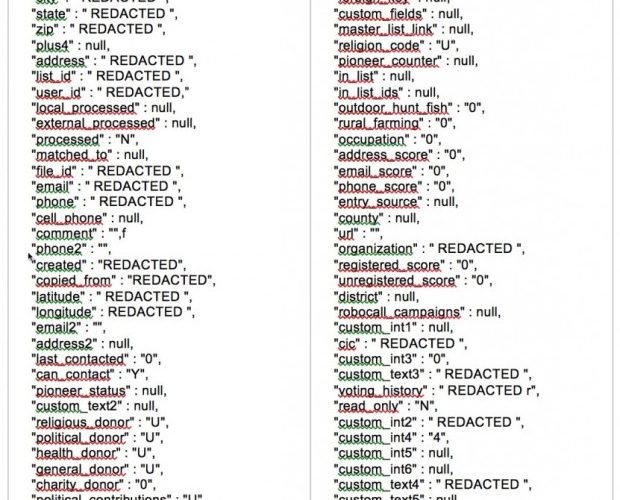
Discovered a new DB containing more than 56 million records of US Voters
A second misconfigured database has been discovered by Chris Vickery containing data of US voters, including 19 million profiles with private information on religion, gun ownership and more. A coupleRead More →