Kazakhstan will force its citizens to install internet backdoors
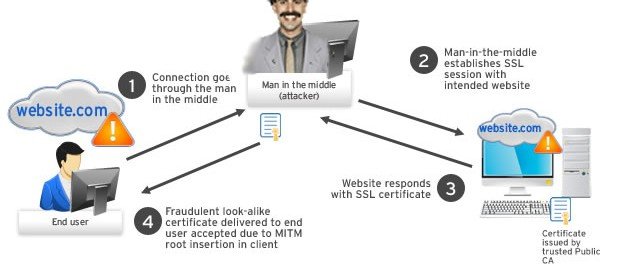
The poorly thought-out and crude surveillance technique could have a devastating effect on the country’s internet security. In less than a month, Kazakhstan will begin enforcing a new law thatRead More →