Catching Up With The ‘EITest’ Compromise, A Year Later
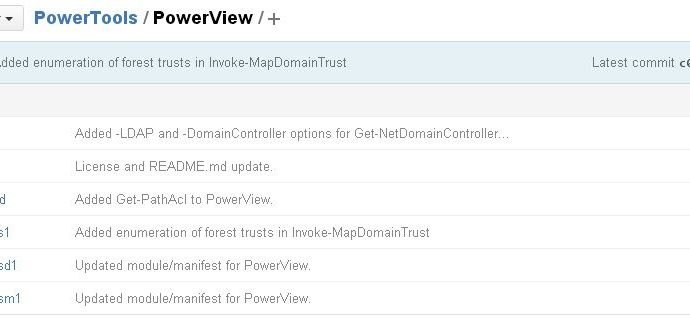
We are seeing dozens of WordPress sites compromised recently with the same malicious code redirecting to the Angler exploit kit. The attack involves conditionally embedded large snippets of code at the bottomRead More →