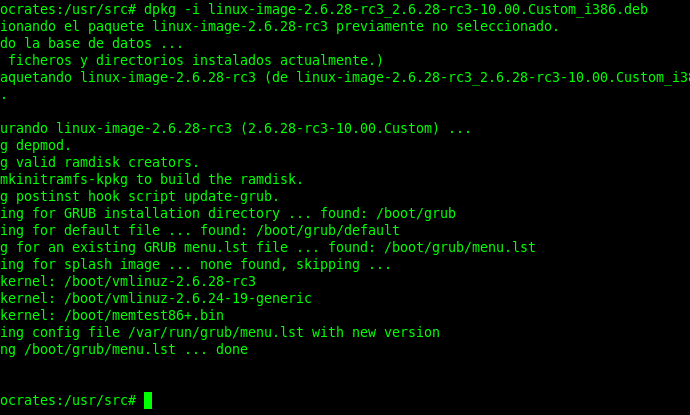
Chikdos cross-platform DDoS botnet hit SQL servers worldwide
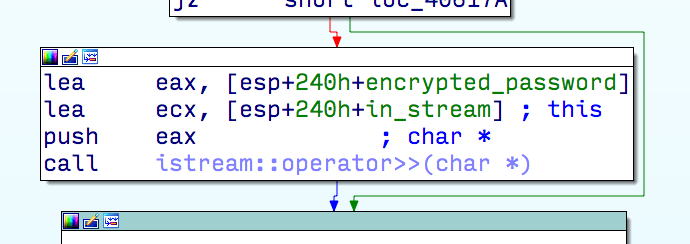
Experts at Symantec have discovered a new variant of the Chikdos DDoS-Trojan that is targeting MySQL servers worldwide. There is a malware in the wild that abuses MySQL Servers forRead More →