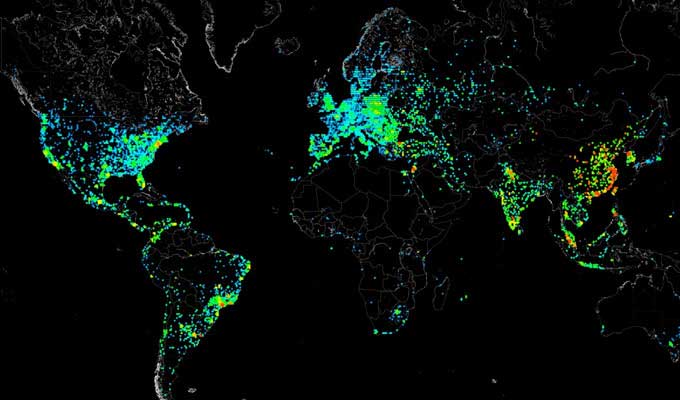
UltraDNS Server Problem Pulls Down Websites, Including Netflix, for 90 Minutes
UltraDNS, a web content delivery service, went down Thursday afternoon, taking with it a number of popular websites, including Netflix and Expedia. The cause of the 90-minute failure was anRead More →