Latest Version of WinRAR Plagued by Dangerous Security Bug
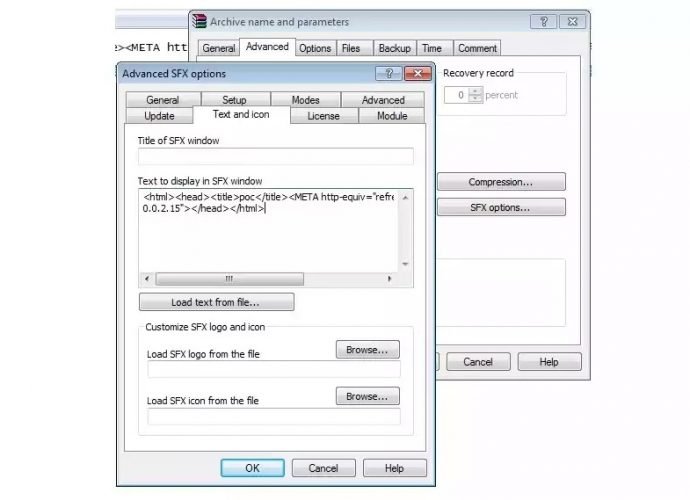
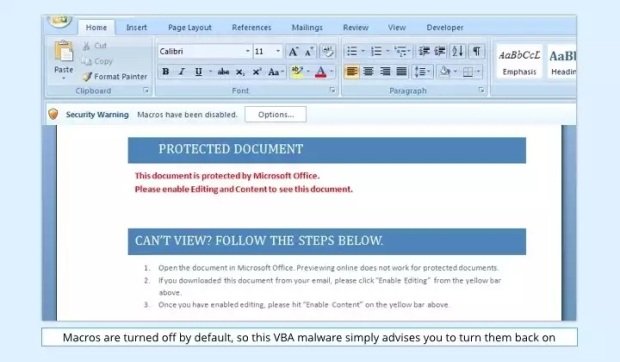
WinRAR, the popular file compression and decompression utility, has a security vulnerability that allows attackers to remotely execute code on the user’s computer when opening an SFX (Self-extracting archive) file.Read More →