Kovter Malware Now Lives Solely in the Windows Registry
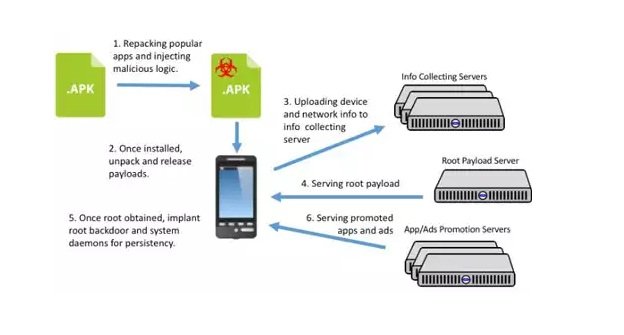
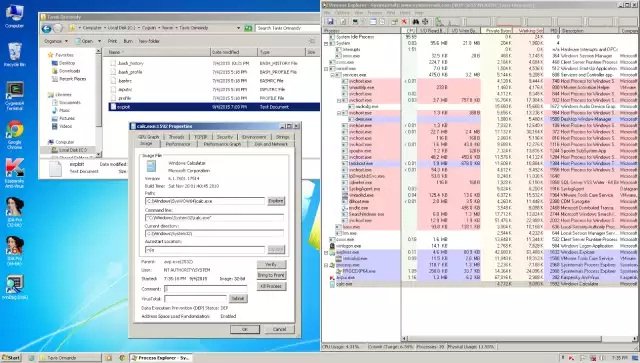
Symantec’s researchers have discovered a new version of the Kovter trojan, which now mimics the Poweliks malware and is able to live on your computer’s registry, without needing to beRead More →