After a group of IT system audit specialists performed an analysis on medical imaging systems connected to the public Internet, it has been concluded that nearly 600 servers, located in 52 different countries, lack the minimum protection measures against unauthorized access.
According to the experts, the analyzed systems do not have update patches to protect them against the exploitation of more than 10k security vulnerabilities, of which at least 500 are high severity flaws. The report was shared by the specialized platform Bleeping Computer.
IT system audit experts, from Greenbone Networks, analyzed more than 2,000 systems for archiving and transmitting images accessible over the public Internet, finding significant drawbacks that can lead to exposure confidential information.
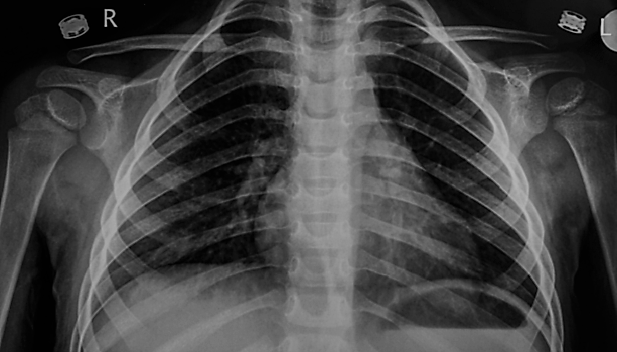
These systems, commonly known as PACS, are used in the medical services industry for the storage and distribution of medical information recovered from devices such as X-ray machines, CT machines, among other devices. Using the standard known as DICOM, these devices transmit, store, print and display medical images.
Greenbone Networks experts used public device search engines on the network and identified 590 PACS servers that were able to be accessed without further mishaps. As a result, experts found more than 24 million medical records. Exposed personal details include:
- Full names
- Birth dates
- Date of analysis
- Type of medical image generated
- Name of the responsible doctor
- Medical institution
- Number of tests per patient
IT system audit specialists fear that a threat actor may use this information to deploy highly sophisticated phishing attacks and social engineering campaigns targeted against specific users to perform identity frauds and economic loses, among other malicious activities.
Experts used a DICOM viewer device to extract information from open PACS servers, reaching 399 million recovered images. Among the countries with the most exposed information were the United States, Italy, France, India and Brazil.
As first mentioned, this research concluded that the systems analyzed could be impacted by more than 10k security issues; about 20% of these flaws have a high severity score. “Nearly 500 of these issues meet the conditions to be considered critical on the scale of the Common Vulnerability Scoring System (CVSS)”, the experts say.
Finally, the research mentions that about 40 PACS servers send data over insecure connection protocols, such as HTTP or FTP, instead of using the industry-standard DICOM protocol. In other words, any user without authentication could access the information stored on these servers.
International Institute of Cyber Security (IICS) IT system audit specialists mention that security risks arising from these findings include identity theft, spear phishing attacks, or theft of medical information access to controlled medicines. Individually, the value of one of these medical records ranges between $250 and $1000 USD in dark web forums.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











