Digital forensics specialists report a new attack method consisting of the use of WAV audio files to hide and deliver backdoors and software for the mining of the Monero cryptocurrency on infected systems.
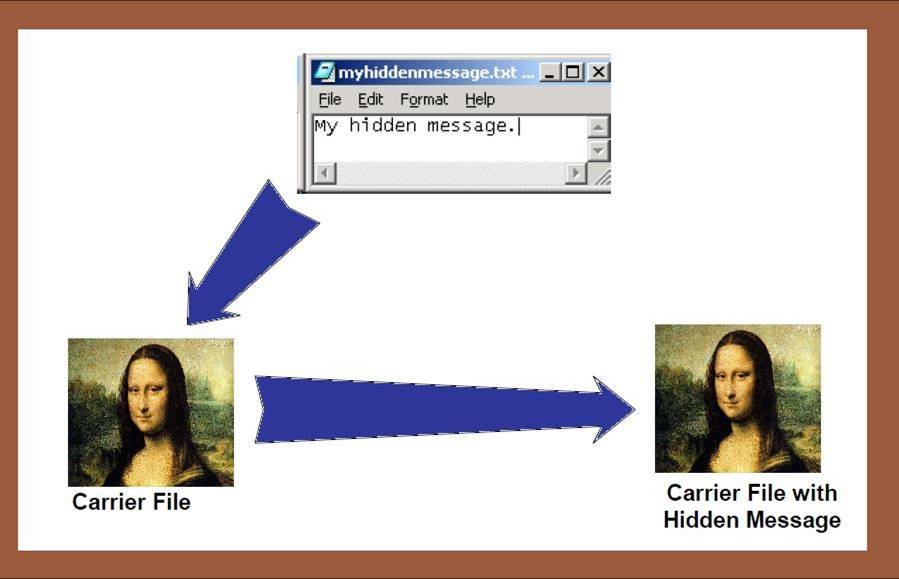
Other variants of this method injected malware by hiding their payloads in JPEG or PNG image files using steganography, a technique widely used by threat actors to hide the malware, so it is curious that this group of hackers has chosen deliver your payloads using malicious audio files.
Last June, Digital forensics specialists at Symantec detected a cell from Turla, a group of Kremlin-backed hackers (also known as Venomous Bear or Wterburg) handing victims the payload that contained the backdoor Metasploit Meterpreter using an audio track in WAV format.
Now, researchers have discovered that an identical steganography method is used to infect devices with XMRig mining software and Metaploit reverse shell code. “These WAV format files are combined with a powerful component to decode and execute the malicious content, which is hidden among the data in the audio file”, the experts mention.
When played, a seemingly conventional music archive could be seen, while other collected samples contained only static. When thoroughly analyzed, the experts detected the payloads of Metasploit and XMRig: “Hackers were planning a cryptojacking and C&C reverse connection operation of considerable scope”, the experts add.
During the analysis, digital forensics experts found that payloads were decoded and executed in three different ways:
- Using loaders that use less significant bit (LSB) steganography to decode and run a PE file
- Loaders that use a rand-()based decoding algorithm to decode and run a PE file
- With loaders that use a rand-() based decoding algorithm to decode and run shellcode
Any of these three methods allows threat actors to successfully hide payloads within any file; they should only avoid corrupting the structure and processing of the container format. In addition, implementing this approach adds a new obfuscation layer, as the code-behind is only revealed in memory, making the payload very difficult to detect.
Although this method of attack is the same used by the Turla hacker group, the digital forensics experts at the International Institute of Cyber Security (IICS) consider it to be somewhat hasty to attribute all these attacks to the same group, since they virtually any hacker could use similar tools and methods.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











